Certificate state and encrypted transport
Track certificate issue, renewal, expiry, and TLS policy at the edge while every approved request moves across an encrypted browser-to-edge-to-origin path.
Keep Certificate State, Policy, and Renewal in One Control Path
Certificate State Visibility
Track issuer, SAN coverage, validity window, and expiry risk so teams can confirm certificate status before a warning or outage reaches customers.
TLS Enforcement at the Edge
Apply protocol and cipher policy where requests enter the platform, then maintain encrypted browser-to-edge and edge-to-origin transport for approved traffic.
Renewal Continuity
Automate issue and renewal while retaining evidence of rollover timing and deployment state so compliance checks and incident reviews stay straightforward.
Read Certificate Health Before It Becomes a Delivery Issue
The certificate state view keeps expiry windows, issuer details, and deployment status visible in one place so teams can catch weak points early.
That visibility reduces emergency rotations and helps operations teams plan renewals around real service windows instead of reacting to browser failures.

Enforce a Verified Encrypted Path for Approved Traffic
Once certificate state is known, TLS policy is enforced at the edge so request transport stays encrypted and consistent from browser through to origin.
This keeps protocol posture and transport controls tied to the same governed path used for day-to-day application delivery.

Renew Without Breaking the Request Path
Renewal is handled as part of normal operations rather than a separate manual event, with state updates tracked through issue, deploy, and active service windows.
Teams can support managed certificates or BYO certificates while keeping renewal history and transport posture aligned.

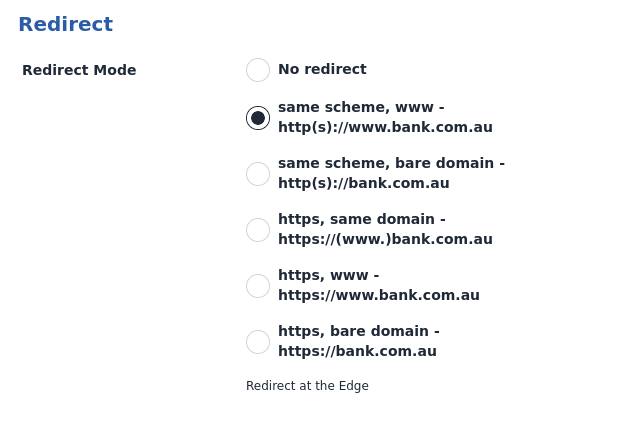
Dashboard Evidence Confirms Policy and Renewal Outcomes
The visual flow explains how certificate state, enforcement, and renewal connect. Dashboard telemetry is used as operational proof that policy is active and certificate operations remain healthy in production.
Security and operations teams can prove that encrypted transport policy is applied and certificate lifecycle events remain on track.
Secure Your Website with TLS
Peakhour's TLS offering gives teams a visible control plane for certificate state, renewal management, encrypted request paths, and audit evidence.

Relevant information from our blog
TLS Fingerprinting: A Primer
What is fingerprinting, and in particular TLS fingerprinting?
Read More
RFC 9460: Enhancing Web Experience
Introducing SVCB and HTTPS records in DNS and their impact on web connectivity.
Read More
HTTP/2 Rapid Reset Attack Deepdive
The technicalities of the HTTP/2 Rapid Reset vulnerability and steps to fortify against DDoS threats.
Read More