Classify, route, and control traffic before it reaches origin
Peakhour turns a noisy mix of browsers, APIs, bots, scrapers, bursts, and expensive requests into edge decisions your operators can explain: allow, challenge, throttle, block, cache, log, or route to the right origin path.

Unknown Traffic Becomes Expensive When It Reaches Origin Unclassified
Application traffic is rarely one clean stream. Human visits, partner APIs, crawlers, scraping tools, credential automation, inventory checks, bursty campaigns, and retry storms all compete for the same origin capacity unless the edge separates them first.
Mixed Intent
Legitimate users, partner services, SEO crawlers, scrapers, credential tools, and monitors can all hit the same routes with very different cost and risk profiles.
Origin Cost Pressure
Unsorted requests inflate compute, database, search, and third-party service usage even when the traffic never becomes revenue or a successful customer workflow.
Operational Guesswork
When decisions happen after the application is already under load, teams lose the chance to explain why traffic was allowed, slowed, redirected, or denied.


Route Each Request by Evidence, Policy, and Cost
Traffic Control moves the decision point to the edge. Peakhour classifies request context, applies policy, and chooses the lowest-friction action that protects origin while preserving clean user and API paths.
-
Classify at the Edge
Use route, session, IP, ASN, geo, device, bot, rate, cache, and request history signals before traffic consumes application resources.
-
Apply Targeted Routing
Send trusted traffic forward, steer region-sensitive requests, shift load away from unhealthy origins, and keep expensive or uncertain traffic on controlled paths.
-
Control Before Capacity Burns
Throttle bursts, challenge suspicious sessions, block confirmed abuse, cache safe responses, and reduce the volume that reaches databases, APIs, and dynamic application tiers.
The Control Loop Stays Visible
Dashboard evidence supports the operating review. Teams can see the traffic class, matched policy, action taken, route outcome, and origin effect without reconstructing the decision from disconnected logs.
Operators can tune the policy loop from observed behavior instead of guessing which traffic caused cost, latency, or origin pressure.
Controls That Shape the Traffic Path
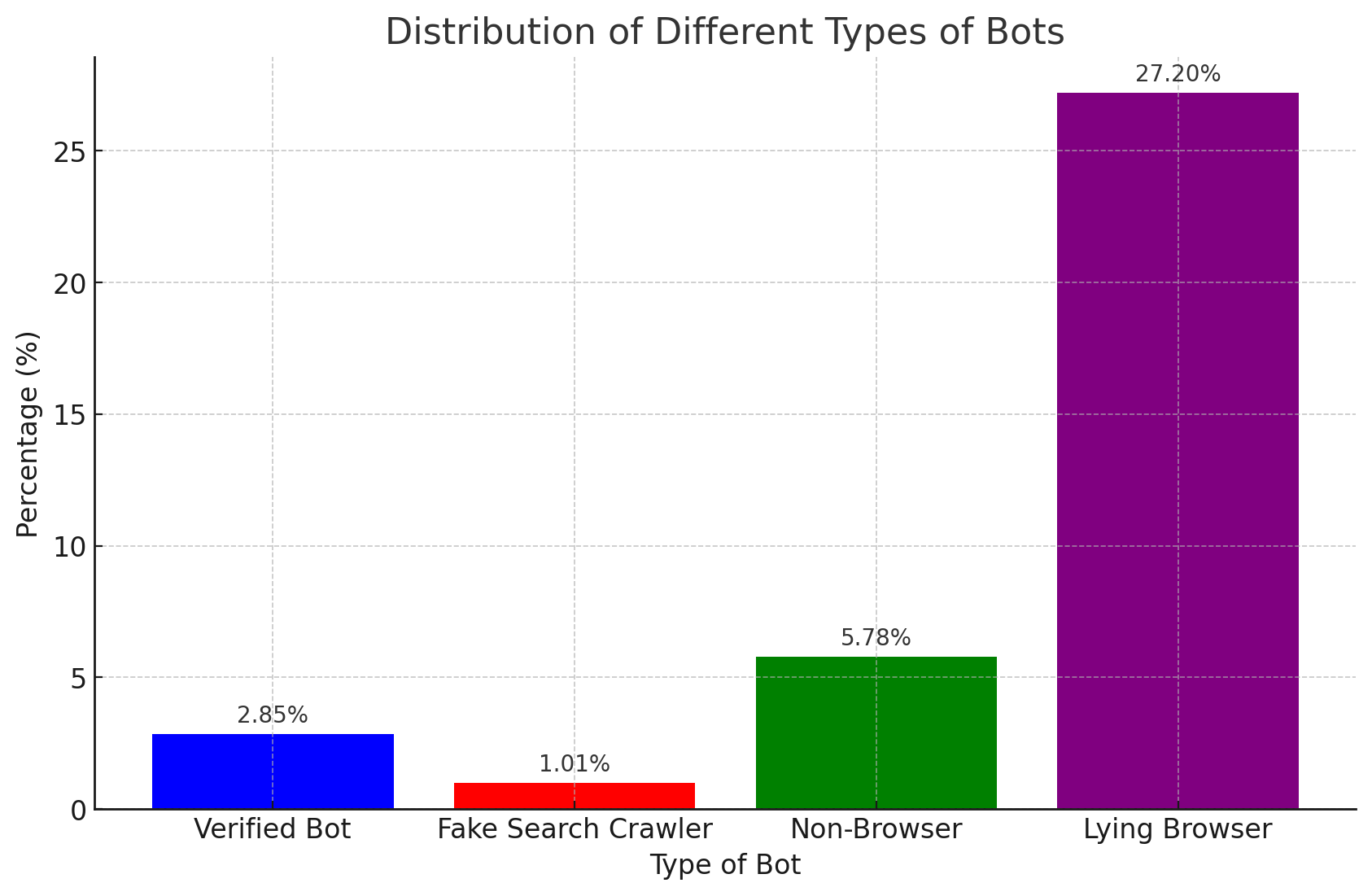
Bot and Browser Classification
Separate normal visitors, verified crawlers, suspicious automation, scrapers, and credential tools before they share the same origin path.
Route-Aware Rate Limits
Limit expensive endpoints by path, identity, IP, geography, method, and request pattern instead of applying one blunt threshold to the whole site.
Policy-Based Routing
Route clean requests to healthy origin paths while steering uncertain traffic through challenge, cache, throttle, or block outcomes.
Origin Shielding
Reduce unnecessary dynamic hits to databases, APIs, search backends, and application servers by enforcing decisions before the request reaches them.
Evidence-Led Tuning
Use enriched logs and dashboard review to adjust thresholds, allowlists, challenges, cache rules, and routing policies with a record of each decision.
Related evidence
Traffic Control Proven in Production
Customer examples that connect Peakhour controls to production outcomes.

Gumtree
Improving Traffic Quality and Reclaiming Platform Control
Gumtree, Australia's leading marketplace, battled significant bot traffic that skewed analytics, enabled scammers, and increased infrastructure costs. Peakhour's bot management solution improved the origin traffic mix, cleaned up campaign analytics, protected A/B testing data, and created a new revenue stream.

Kitchen Warehouse
COVID-19 Traffic Surge Success
How Australia's #1 online kitchenware retailer thrived during COVID-19's unprecedented traffic surge and achieved 150% revenue growth with Peakhour's performance solutions.
Explore the Controls Behind Traffic Decisions
Bot Management
Classify browser, crawler, scraper, and automation behavior before it drains application capacity.
Advanced Rate Limiting
Throttle expensive or abusive request patterns by route, identity, geography, method, and evidence.
Load Balancing
Route clean traffic to healthy origins while failover and geography policies keep services available.
Send Cleaner Traffic to Origin
Bring your current traffic mix. Peakhour can help classify what is costing money, decide what should route forward, and keep the control loop visible.

Relevant information from our blog

Layer 7 DoS attacks and Full Page Caching
Discover how Full Page Caching can help mitigate layer 7 DoS attacks.
Read More
IP Threat Intelligence
Discover and block threats through data enrichment using managed IP reputation lists.
Read More
Google Chrome's "IP Protection" and Online Privacy
An exploration of Google Chrome's new "IP Protection" feature, its promise of enhanced privacy.
Read More