Signal coverage: Validate identity, TLS, bot, and cache fields before they reach downstream tools.
Enriched logs from edge decision to analysis
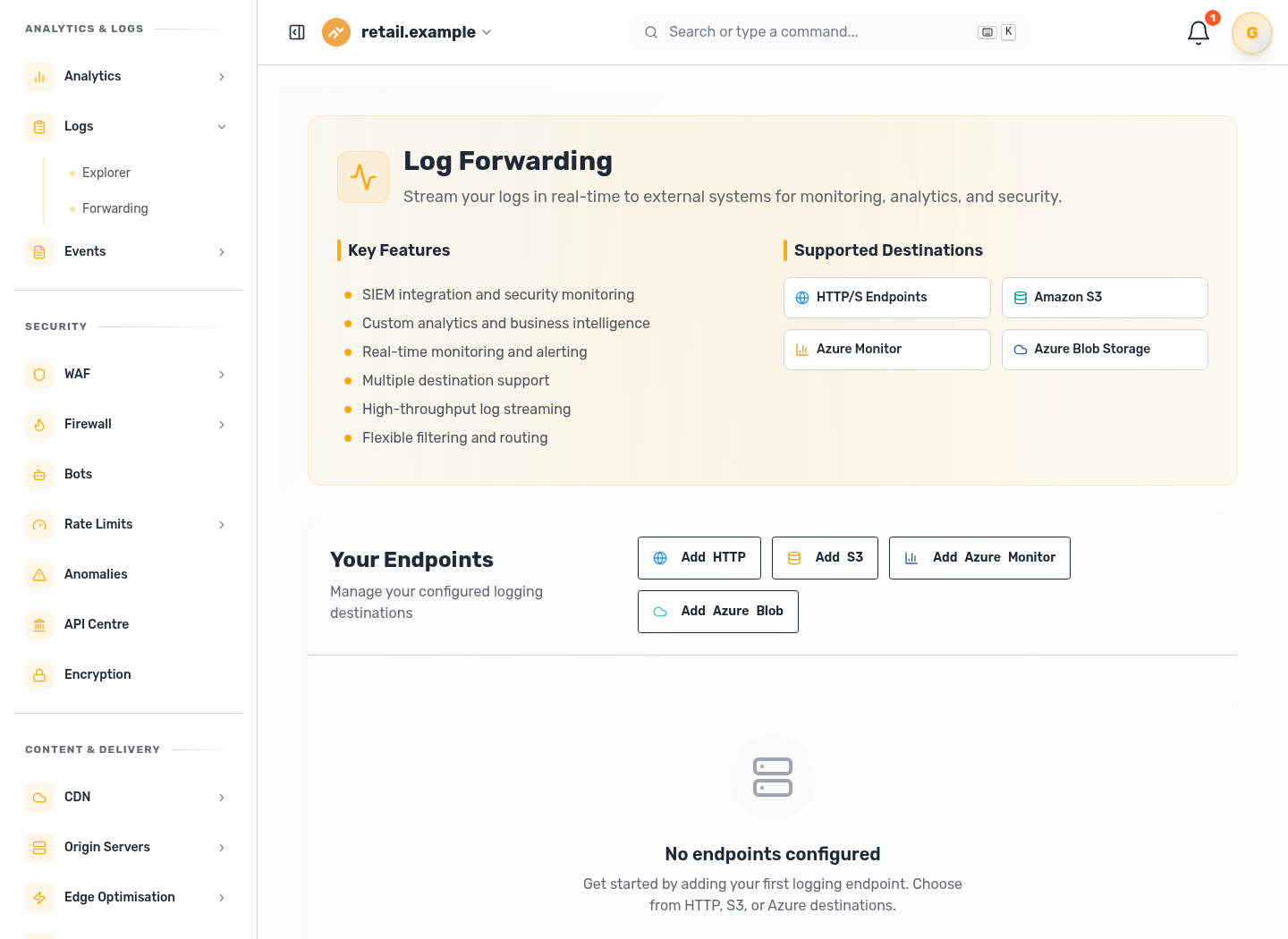
Stream request logs enriched with identity decision, certificate state, TLS path, bot and cache signals to your SIEM, object store, or observability pipeline.
From Edge Decision to Searchable Evidence
Real-time Event Stream
Each request event is forwarded immediately, so operations teams can investigate incidents while access, TLS, cache, and threat context is still current.
Enrichment in-line
Logs carry identity outcome, certificate status, TLS policy, encrypted path details, bot classification, and cache state as one cohesive request record.
Destination Flexibility
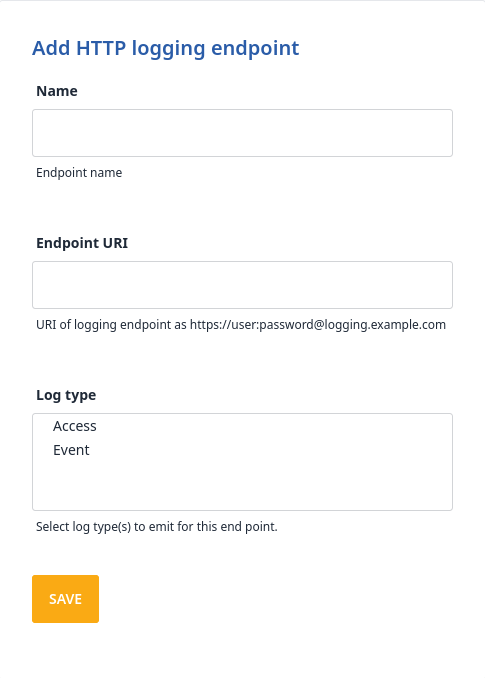
Forward to S3, Azure Sentinel, Azure Monitor, Google Cloud Observability, or HTTP endpoints without rebuilding your analysis workflow.
Preserve Full Request Context in One Pipeline
Peakhour turns isolated edge signals into a single event stream so investigators can trace what happened without stitching together separate tools.
Access decisions, TLS status, cache outcomes, and bot intelligence stay tied to the same request as it moves from edge handling to downstream analysis.
Deliver the Same Evidence to the Tools Your Team Already Uses
The forwarding path keeps data intact from pipeline to destination, so SIEM and observability teams see the same enriched request facts used at the edge.
This makes incident triage, compliance reporting, and threat hunting consistent across platform operations and security workflows.
Dashboard Evidence Confirms the Stream is Actionable
Concept diagrams establish the forwarding model. The product view then verifies that enriched log data is flowing, searchable, and tied to endpoint configuration.
Investigation readiness: Move from edge decision to destination analysis without losing request context.
Transform Your Log Analysis
Peakhour Log Forwarding moves enriched request evidence into the systems your operations and security teams already use for investigation, compliance, and response.

Relevant information from our blog

IP Threat Intelligence
Discover and block threats through data enrichment using managed IP reputation lists.
Read More
An Overview of JA4+ Network Fingerprinting and Its Implications
An in-depth exploration of the JA4+ network fingerprinting method, its applications, and its role in cybersecurity.
Read More
A Risk Based Approach To Vulnerability Scoring
An in-depth exploration of EPSS, its data-driven approach to assessing cybersecurity threats, and how it complements CVSS.
Read More

