Protect Patient Services Without Breaking Care
Peakhour puts patient portals, telehealth, appointment systems, clinical APIs, and provider apps behind one edge control path so privacy, availability, and application protection stay connected.

Healthcare Risk Sits Across the Same Request Path
Patient Privacy Exposure
Patient portals, test results, intake forms, billing workflows, and clinical APIs all carry sensitive health information that needs route-aware protection and evidence.
Care Availability Pressure
Telehealth, booking, prescription, and patient-access services cannot disappear during DDoS floods, bot surges, or origin instability.
Application Abuse and Exploits
Credential stuffing, API probing, scraper traffic, form abuse, and vulnerability scans move through normal healthcare application routes.
Every Patient Request Carries Security, Privacy, and Uptime Context
A login attempt, telehealth session, appointment lookup, or API request may need a different control. Healthcare teams need to know who is asking, what route is being touched, whether the service is under pressure, and what evidence will remain for review.
Sensitive Routes Need Stronger Decisions
Patient records, payments, provider administration, and clinical APIs should receive stricter treatment than public education content.
Downtime Becomes a Care Problem
Availability controls need to absorb attack traffic while keeping clean patient and provider sessions moving toward live services.
Compliance Needs the Request Story
Security and privacy reviews need decision records, action history, and exportable telemetry instead of disconnected screenshots or generic alerts.

One Edge Decision Before Care Access
Peakhour evaluates healthcare traffic at the edge before it reaches protected applications. Clean requests continue to patient and provider services; suspicious sessions can be challenged, rate-limited, blocked, or logged with the evidence needed for review.
-
Classify the Healthcare Route
Separate public content, patient portal traffic, telehealth sessions, administrative paths, and API calls before choosing a control.
-
Apply Coordinated Protection
Combine WAF, API security, bot management, credential checks, rate limits, DDoS mitigation, and access policy in the same decision path.
-
Retain Operational Evidence
Keep the route, signal, decision, action, and timing data that security, privacy, and operations teams need after an incident or audit question.
Protect Patient Privacy at the Application Edge
Healthcare privacy depends on how sensitive requests are handled before they reach patient systems. Peakhour helps protect portals, forms, account flows, and clinical APIs with controls that understand route context instead of treating every request alike.
Privacy-focused controls include:
- Patient portal protection: Defend login, password reset, billing, appointment, and results routes from account abuse.
- API and form security: Apply WAAP and schema-aware controls to clinical data exchange, intake, and partner integrations.
- Access evidence: Preserve policy decisions and request context for privacy review, incident analysis, and audit support.

Keep Telehealth and Patient Access Available
Availability is part of patient trust. Peakhour's global edge absorbs volumetric floods, evaluates Layer 7 request pressure, and keeps clean healthcare traffic on a fast path to critical services.
DDoS, bot, rate, and load controls work together so attackers do not force teams to choose between blocking abuse and keeping appointment, telehealth, and portal flows online.

Application Protection That Privacy and Operations Can Share
The control path ties patient-data protection, uptime, and application security into one operating model. Each team can see how a request was classified, what action was taken, and which service was protected.
-
Security teams: Block exploit attempts, bot traffic, credential attacks, and abusive API calls before they reach patient-facing services.
-
Privacy teams: Review access decisions and evidence attached to sensitive routes that carry patient or provider data.
-
Operations teams: Keep telehealth, booking, and patient portal traffic available during attack or surge conditions.
-
Application teams: Tune policies by route so public information, account access, and clinical APIs receive the right level of control.

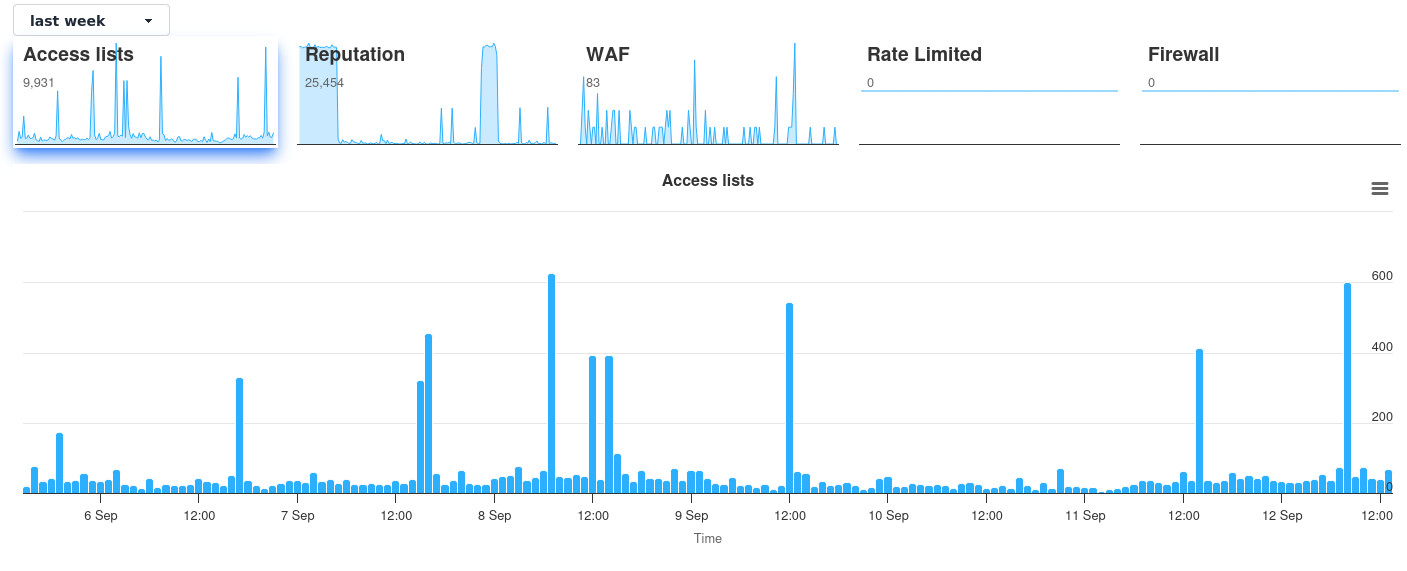
Dashboard Evidence Supports the Healthcare Control Path
Roadmap visuals explain how healthcare traffic is governed. Dashboard evidence then shows whether policy is working under live pressure, with security events, actions, and trends available for operational review.
The dashboard is supporting proof, not the page's main visual. It confirms the same privacy, availability, and application protection story shown in the concept visuals above.
Map Healthcare Traffic to Edge Controls
Review your patient portal, telehealth, clinical API, and public site routes against the controls and evidence each one needs.

Relevant information from our blog

Breached Credentials Protection: Advanced Account Security for Application Platforms
Comprehensive guide to breached credentials protection within modern application security platforms. Learn how to defend against credential stuffing attacks using advanced risk profiling and contextual security measures.
Read More
Why Multi-Factor Authentication Alone Can't Stop Account Takeovers
As cybercriminals employ AI and residential proxies to bypass multi-factor authentication, businesses must adopt a multi-layered security approach to protect against account takeovers.
Read More
Enterprise DDoS Protection: Lessons from Microsoft 365 Attack for Application Security
Analysis of the Microsoft 365 DDoS attack reveals critical lessons for enterprise application security platforms.
Read More