Schema evidence: Prioritize drift and validation failures by route.
API Protection Platform
Discover the full API landscape, validate REST, GraphQL, and WebSocket requests against expected schemas, monitor API attacks, and keep route-level observability evidence close to every edge decision.

Hidden Risks in Your API Landscape
APIs are the backbone of modern applications, but unmanaged, undocumented, and unsecured endpoints create attack paths that are hard to prioritize without a live inventory and route-level exposure context.
Shadow & Zombie APIs
Undocumented or deprecated APIs that remain active, creating unmonitored entry points for attackers and increasing liability exposure for your organization.
Business Logic Flaws
Attackers exploiting legitimate API functions for malicious purposes, potentially leading to fraudulent transactions and service abuse that directly impacts your revenue.
Data Exposure
Improperly configured APIs leaking sensitive customer, financial, or proprietary data, resulting in regulatory penalties and loss of competitive advantage.

Discover, Validate, and Enforce
Peakhour connects endpoint discovery, schema validation, authenticated request handling, and policy enforcement so API protection follows each route from first sighting to active protection.
-
API Discovery
Continuously discover and catalogue REST, GraphQL, and WebSocket APIs, including shadow and zombie endpoints, with ownership, schema state, and current risk.
-
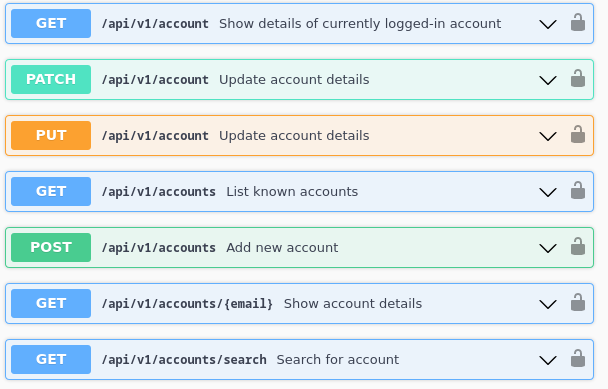
Schema Compliance & Validation
Enforce strict adherence to OpenAPI/Swagger specifications for REST APIs, apply GraphQL depth controls, and bind WebSocket traffic to authenticated context.
-
Threat Protection
Protect against the OWASP API Top 10, including injection attacks, broken authentication, and data exposure, with policy decisions and evidence captured at Peakhour Edge or alongside the edge you already run.
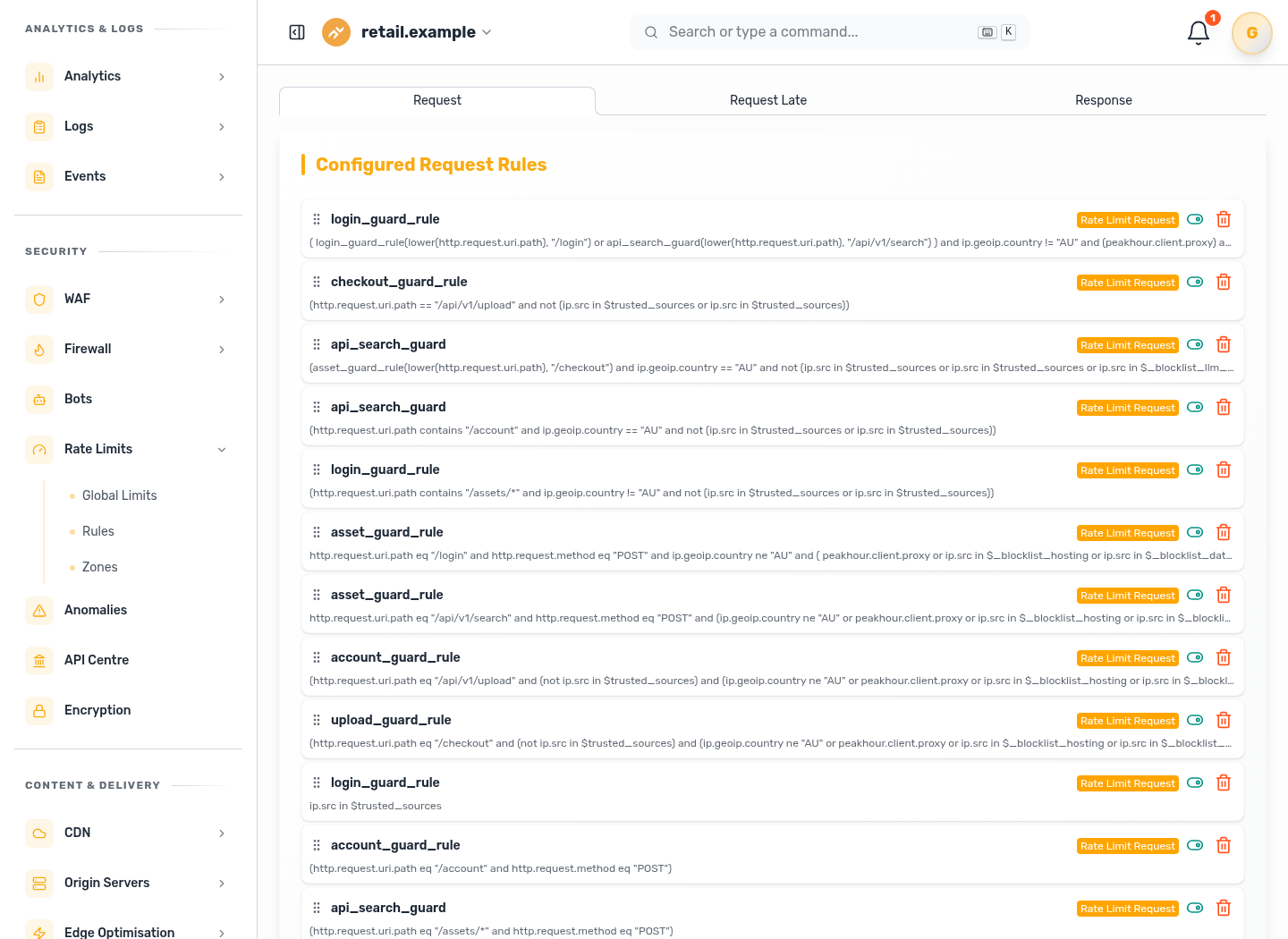
API Risk and Attack Monitoring Evidence
Every protected route produces evidence for security and platform teams: endpoint risk, schema violations, authentication failures, blocked attack classes, latency, and clean traffic trends.
Attack monitoring: Connect API abuse evidence to authentication failures, latency, and clean traffic trends.
Related evidence
API Risk Reduced in Production
Customer examples that connect Peakhour controls to production outcomes.
Secure Your APIs with Enterprise-Grade Protection

Relevant information from our blog

Headless Commerce Security: API Protection for Modern E-commerce Architectures
Comprehensive analysis of security challenges in headless commerce and Single Page Applications.
Read More
When Bots Are Your Primary Users
An exploration of how AI agents are reshaping API design principles and why we must evolve our approach to serve both machine and human consumers.
Read More
Advanced Rate Limiting for API Security
How advanced rate limiting protects modern applications and APIs from sophisticated threats.
Read More
Price transparency needs governed automation
Price comparison increasingly depends on current web and API data. See how governed automation separates intended access from abusive extraction.
Read More