Stop account and payment abuse before it becomes loss
Peakhour scores login, API, checkout, transfer, and verification traffic at the edge so financial teams can challenge risky sessions, block automation, and keep trusted customers moving.

Where Financial Abuse Shows Up
Credential Stuffing and Takeover
Detect breached credentials, residential proxy rotation, impossible client changes, and repeated login attempts before attackers reach balances, cards, or personal data.
Payment and Transfer Fraud
Score high-value actions with account age, device history, proxy reputation, velocity, card attempts, and session behaviour before money or goods move.
Verified Browser Trust
Add a verified browser signal before sensitive login, payment, transfer, and verification actions so fraud teams have another reviewable signal before money or account state changes.
SMS and Verification Abuse
Rate-limit costly verification flows, identify automated sign-up patterns, and stop SMS pumping fraud before it burns budget or pollutes customer records.
Attackers Blend into Real Banking Traffic
A login, card check, API call, or payment attempt can look valid in isolation. The financial services challenge is connecting identity, network, device, behaviour, and transaction context quickly enough to choose the right control.
Low-friction Abuse
Credential stuffing, card testing, and account creation attacks reuse normal application paths instead of obvious exploit traffic.
Direct Business Cost
Fraud review, SMS charges, chargebacks, support load, and infrastructure pressure become operational cost even when core systems stay online.
Customer Trust at Risk
False blocks hurt adoption, while missed abuse damages confidence in accounts, cards, payments, and digital service availability.

One Edge Decision Before the Sensitive Action
Peakhour turns fraud, account, and transaction context into a recorded edge decision before protected actions complete. Clean customers continue to account, payment, and open-banking flows; risky sessions are stepped up, rate-limited, blocked, or logged with the evidence needed for review.
-
Connect Account and Fraud Signals
Attach IP intelligence, proxy detection, credential exposure, verified browser, device, behaviour, and route context to the account or transaction request being evaluated.
-
Choose the Right Control
Allow, challenge, block, throttle, or log based on action risk and customer value before login, verification, payment, transfer, or open-banking flows complete.
-
Keep Reviewable Evidence
Retain the signals, route, score, and policy action that fraud, security, and compliance teams need for investigation, reporting, and control tuning.
Regulated Paths Need Clear Evidence
Financial institutions need more than a block count. They need to show how sensitive paths are protected, which signals drove each action, and whether controls preserve availability for legitimate customers.
Peakhour helps support APRA CPS 234, PCI DSS, CDR, and internal risk obligations with:
- Policy traceability: Record the signals, score, route, and action behind each challenged or blocked request.
- Protected API surfaces: Apply WAAP, bot, and rate controls to REST, GraphQL, authentication, and open-banking endpoints.
- Audit-ready telemetry: Stream enriched logs to security, fraud, and compliance workflows.
- Australian operations: Work with an Australian-owned provider for local support and data-sovereignty expectations.

Operational Evidence for Fraud Review
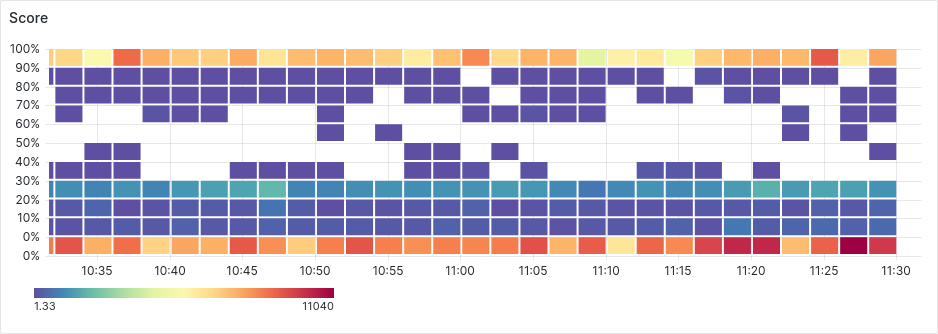
Fraud and security teams need to see whether policy is working under live pressure. Request evidence backs each edge decision with timing, prediction scores, and action history.
Risk decisions stay connected to the facts that made them, so teams can investigate abuse without rebuilding context from raw logs.
Outcomes for Financial Services Teams
The result is not another generic security layer. It is a control path that ties abuse prevention, customer experience, and compliance evidence together around high-value financial actions.
-
Fraud teams: Focus review on risky sessions with evidence attached, not long queues of disconnected alerts.
-
Security teams: Protect login, API, payment, and verification endpoints with coordinated WAAP, bot, and rate controls.
-
Digital teams: Preserve fast paths for trusted customers while challenging suspicious actions at the right moment.
-
Compliance teams: Export decision records that help explain how controls are applied to regulated data and transaction paths.

Protect High-Value Financial Actions
Map your login, payment, transfer, and verification flows to edge controls that can act before fraud reaches the business.

Relevant information from our blog

APRA Cybersecurity Guidelines: Application Security Requirements for Australian Financial Services
Comprehensive guide to APRA cybersecurity requirements for Australian financial institutions.
Read More
SMS Pumping Fraud: How Attackers Turn Verification Flows into Cost
How automated sign-up and verification abuse creates direct telecom cost and what application teams can do to detect it earlier.
Read More
The Iconic is the latest Account Takeover victim in the news
Popular Australian fashion website TheIconic recently suffered reputational damage from fraudsters placing orders after an account takeover. Learn how this happens and what you can do to stop it.
Read More