Mitigation actions: Confirm block and challenge decisions against live traffic.
DDoS Protection & Mitigation
Detect abnormal request behavior, absorb high-volume surge traffic, and preserve application availability through Peakhour Edge or an existing edge augmented with Peakhour intelligence.

Keep Service Availability Under Layer 7 Pressure
Absorb Surge Pressure at the Edge
Defend against high-volume request surges at Peakhour Edge or through an existing edge path augmented with Peakhour controls.
Mitigate Layer 7 Flood Behaviour
Suppress HTTP flood patterns, Slowloris traffic, and route-level abuse before origin resources are consumed.
Sustain Operations with Evidence
Keep clean user traffic moving while logging mitigation outcomes for response, tuning, and post-incident review.
Availability Risk Arrives as Mixed Traffic, Not a Single Attack Signature
Service disruption events usually combine high-volume bursts, Layer 7 floods, and automated request noise. Teams need one mitigation path that separates abusive traffic from legitimate traffic before origin capacity is exhausted.
Distributed Floods Bypass Simple IP Thresholds
Modern attack traffic rotates networks, clients, and headers, so static per-IP limits alone often miss coordinated surge behaviour.
Origin Capacity Is Consumed Before Manual Response
If mitigation depends on human reaction during an incident, legitimate user sessions can degrade before controls are tightened.
Incident Review Fails Without Request-Level Proof
Without consistent mitigation evidence, teams cannot verify which traffic was blocked, challenged, or allowed during an event.

One Mitigation Path from Detection to Clean Delivery
Peakhour combines anomaly detection, rate controls, bot signals, and WAAP policy in one decision flow so attack traffic is filtered while healthy requests continue to application routes.
-
Detect Abnormal Request Behaviour Early
Continuously analyse request patterns to identify flood behaviour before it escalates into customer-visible downtime.
-
Apply Layered Controls per Request Context
Use thresholds based on network, geography, headers, and behavioural attributes rather than relying only on source IP counting.
-
Deliver Clean Traffic with Operational Continuity
Block or challenge abusive request classes while preserving availability for trusted users and business-critical paths.
-
Keep Mitigation Evidence Ready for Review
Retain mitigation outcomes and trend telemetry so security and platform teams can tune controls after each incident window.
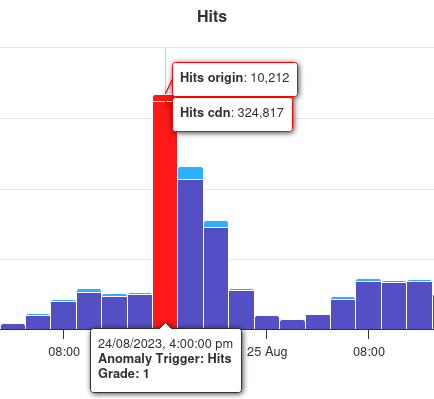
Operational Proof of Layer 7 Mitigation
The diagrams explain the mitigation path. Dashboard telemetry is the proof layer: it shows flood pressure, control decisions, and whether clean application traffic stayed available.
Post-incident review: Use one evidence stream for response, tuning, and reporting.

Choose the Next DDoS Control
Stop Layer 7 DDoS Attacks
Move from attack pressure to edge actions that can be tuned and reviewed during an incident.
Advanced Rate Limiting
Set route, fingerprint, geography, header, and behaviour limits instead of relying on IP-only thresholds.
Bot Management
Score the automation behind Layer 7 floods and apply challenges or blocks with request evidence.
WAAP and WAF Controls
Keep WAF, API, bot, rate, and DDoS decisions in one reviewable application-security path.
Related evidence
DDoS Mitigation Proven in Production
Customer examples that connect Peakhour controls to production outcomes.

Kitchen Warehouse
COVID-19 Traffic Surge Success
How Australia's #1 online kitchenware retailer thrived during COVID-19's unprecedented traffic surge and achieved 150% revenue growth with Peakhour's performance solutions.

Stone & Chalk
Fintech Hub Enterprise Security
How Australia's leading fintech hub secured hundreds of startups with enterprise-grade application security, zero-day vulnerability protection, and comprehensive threat management.
Guarantee Your Application Availability

Relevant information from our blog

Enterprise DDoS Protection: Lessons from Microsoft 365 Attack for Application Security
Analysis of the Microsoft 365 DDoS attack by Storm-1359 reveals critical lessons for enterprise application security platforms.
Read More
HTTP/2 Rapid Reset Attack Deepdive
The technicalities of the HTTP/2 Rapid Reset vulnerability and steps to fortify against DDoS threats.
Read More
Layer 7 DDoS Protection: Application Security Through Strategic Caching
Comprehensive guide to Layer 7 DDoS protection using strategic caching within application security platforms.
Read More