Incident review: Use request-level context instead of stitching disconnected screenshots together.
Application Security Platform
App Security Platform
Peakhour protects applications and APIs with one policy plane for WAF, API rules, bot signals, rate limits, DDoS controls, clean app delivery, and evidence logs across Peakhour Edge or your existing edge.
One application security plane for WAAP, API rules, bot signals, rate limits, DDoS, clean delivery, and evidence logs.

Where Application Risk Actually Lands
Application security failures are usually mixed-path events: exploit attempts against app routes, API misuse, and automated abuse arriving together. WAAP decisions need shared context so controls are aligned before traffic reaches origin.
Exploit and Abuse Traffic Share the Same Surface
SQLi, XSS, API payload abuse, credential attacks, and scraping pressure often target the same routes. Splitting these controls across disconnected tools leaves blind spots and slow incident triage.
Availability Pressure Hides Inside L7 Noise
Layer 7 floods, route hammering, and retry storms can look like normal bursts unless bot posture, rate controls, and DDoS guardrails are evaluated in one request path.
Security Teams Need Defensible Evidence
Without route-level proof for blocked requests, challenge outcomes, and clean delivery, post-incident review turns into screenshot hunting instead of confident policy refinement.


One WAAP Control Path from Request to Outcome
Peakhour applies WAF inspection, API validation, bot and identity signals, rate controls, and DDoS decisions in a single control path. The same policy model works at Peakhour Edge or alongside your existing edge stack.
-
WAF Enforcement for Known and Emerging Exploits
Block OWASP-class attacks and suspicious payload behavior before origin execution, with adaptive controls that reduce bypass drift as traffic patterns change.
-
API and Bot Signals Stay in the Same Decision Plane
Schema checks, authentication context, and bot posture combine per request so challenges, blocks, and allow actions stay consistent across web and API routes.
-
Rate and DDoS Controls Protect Availability
Control request surges with route-aware limits and edge mitigation so application availability is preserved without overblocking legitimate users.
-
Clean Delivery and Audit Trails Close the Loop
Allowed traffic is delivered with full request context while blocked and challenged events remain queryable for incident response and compliance reporting.
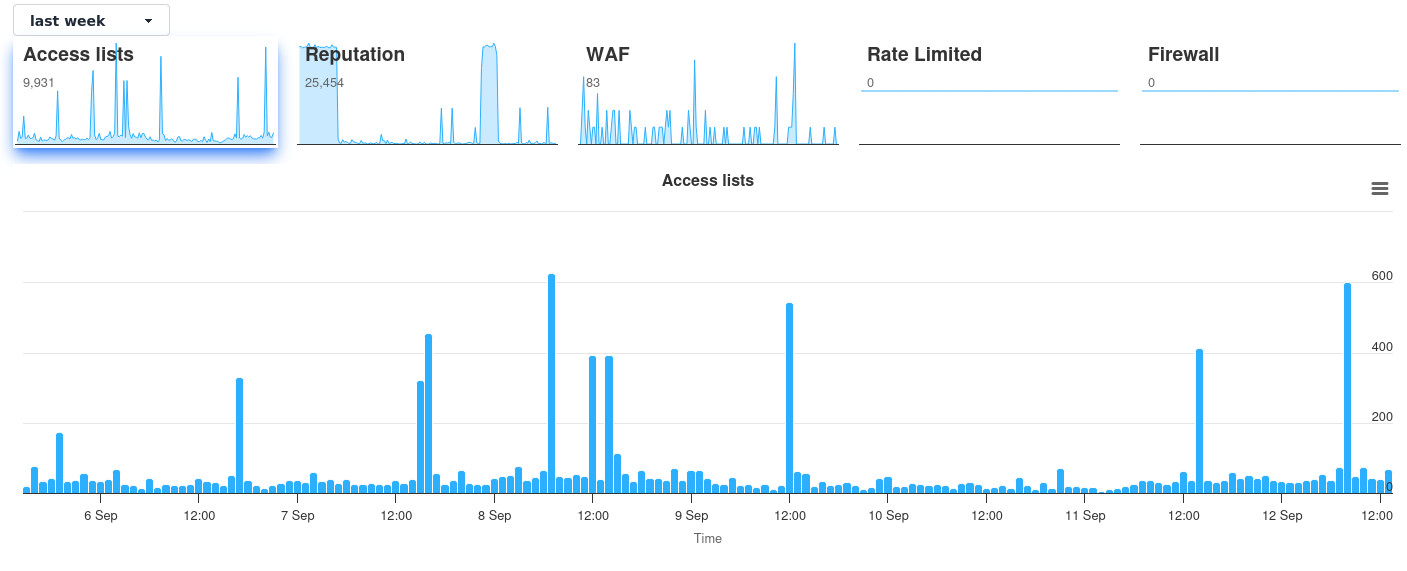
Operational WAAP Evidence in One Board
Security, platform, and incident responders work from the same evidence stream: blocked exploit classes, API validation failures, challenge outcomes, surge controls, and clean traffic delivery.
Policy governance: Keep control decisions and rollback evidence close to the traffic record.

Related evidence
Application Security Proven in Production
Customer examples that connect Peakhour controls to production outcomes.

National Gallery Australia
Government Security Compliance & Bot Management
How Australia's National Gallery achieved government security compliance with advanced bot management, DDoS protection, and content scraping controls whilst improving digital visitor experience.

Stone & Chalk
Fintech Hub Enterprise Security
How Australia's leading fintech hub secured hundreds of startups with enterprise-grade application security, zero-day vulnerability protection, and comprehensive threat management.
Customer proof
Peakhour's security solutions have transformed our online presence. We've seen a significant improvement in customer trust and a dramatic reduction in security incidents.
Jean Akkard, E-commerce Director
Supported Technologies and Integrations







Explore Our Security Platform
Secure Your Applications Today

Relevant information from our blog

ModSecurity’s End-of-Life: Implications for Peakhour and Customers
ModSecurity's end-of-life marks a pivotal moment in application security evolution. Discover how modern Application Security Platforms are advancing beyond traditional WAF approaches.
Read More
APRA Cybersecurity Guidelines: Application Security Requirements for Australian Financial Services
Comprehensive guide to APRA cybersecurity requirements for Australian financial institutions.
Read More
HTTP Security Headers: Essential Browser Protection for Web Application Security
Comprehensive guide to HTTP security headers for protecting web applications from client-side attacks.
Read More