Keep Checkout Fast While Abuse Stays Out
Peakhour protects product, account, cart, and payment paths from fraud, scraping, credential stuffing, and peak-event pressure without slowing clean shoppers.

Where Storefront Abuse Hits Revenue
Payment Fraud Prevention
Reduce financial losses from fraud by up to 90% and eliminate costly chargebacks through advanced behavioural analysis, risk scoring, and residential proxy detection.
Inventory & Content Protection
Protect your competitive advantage and prevent revenue loss from competitor price scraping, inventory hoarding, and content theft while allowlisted customers and clean sessions keep reaching product and checkout pages.
Account Security & Customer Protection
Defend customer accounts against credential stuffing, brute force attacks, and Magecart while enforcing PCI DSS and GDPR/CCPA controls on payment and account paths.
Customer Data Protection & Compliance
PCI DSS Compliance
Protect cardholder data and secure payment processing paths without slowing legitimate checkout sessions.
GDPR/CCPA Boundaries
Apply privacy-aware controls to account, consent, and customer data paths while preserving clean shopper traffic.
Encrypted Session Control
Keep credentials, cart state, and payment actions protected while detecting takeover and session abuse patterns.
Abuse Reaches the Same Paths Shoppers Use
E-commerce abuse is not a background IT issue. It directly interrupts product discovery, checkout completion, and customer trust across your highest-value sessions.
The damage shows up in the operating metrics commerce teams already watch.
- Slow performance, account takeovers, and security incidents erode customer trust and push shoppers to competitors.
- Fraudulent transactions create chargeback cost while bot traffic increases infrastructure pressure.
- Automated traffic distorts marketing data, product demand signals, and campaign attribution.
- Inventory hoarding makes products appear unavailable and checkout disruption turns intent into abandoned carts.

Regulated Checkout Needs Route-Aware Controls
Peakhour applies layered controls from request admission to checkout completion so compliant, legitimate customers stay fast while hostile sessions are challenged or blocked.
Payment, privacy, account, and bot controls stay connected to the same request path.
- Cardholder data and payment processing paths remain protected without adding friction to clean checkout sessions.
- Privacy boundaries and consent-aware handling are enforced on account and customer-data routes.
- Customer credentials, cart state, checkout actions, and payment requests remain encrypted in transit.
- Trusted sessions continue while takeover attempts, inventory hoarding, and credential stuffing are disrupted.
- Suspicious access patterns and sensitive data exposure stay visible for review.

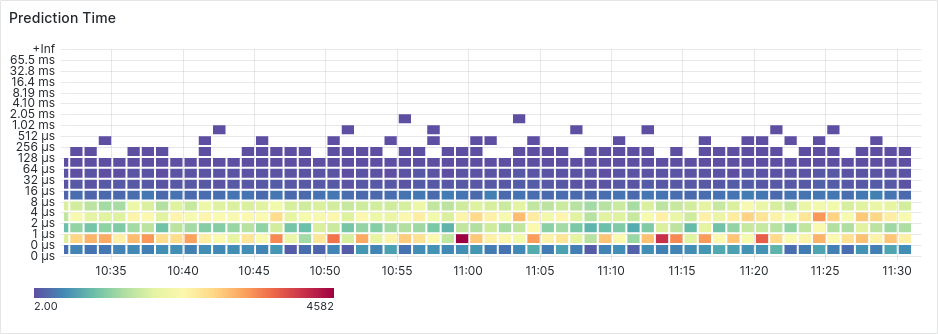
Operational Evidence During Peak Events
Controls are only useful if they hold under pressure. This dashboard evidence shows the live decision stream used to separate trusted shoppers from abusive automation during high-traffic retail windows.
Security and commerce teams share one view of pressure points, mitigation outcomes, and customer experience protection.
Conversion Improves When the Path Stays Clean
-
Legitimate shoppers keep moving through product, cart, account, and payment flows.
-
Risky payment and account traffic is intercepted before it becomes financial loss.
-
Traffic surges and attack spikes are absorbed without storefront degradation.
-
Marketing and merchandising decisions rely on less bot-skewed session data.
-
The same control fabric supports both conversion speed and abuse resistance.

Commerce Platforms Keep Their Native Flow
-
Magento stores can combine full-page caching, image optimisation, and enterprise security on product, cart, and checkout paths.
-
WordPress and WooCommerce storefronts can improve conversion speed while adding account and bot protection.
-
Drupal Commerce deployments can use advanced caching and security controls without rebuilding the application.
-
PrestaShop and OpenCart flows can preserve dynamic cart behaviour while edge controls protect clean sessions.
-
Headless commerce architectures can apply API security to product, account, cart, payment, and customer-data routes.
-
Custom platforms can connect through Peakhour APIs while keeping commerce-specific control evidence visible.

Protect Revenue Paths Before the Next Peak