Keep Citizen Services Online With Evidence Behind Every Control
Peakhour protects public-facing portals, agency APIs, emergency information sites, and grant or licensing workflows at the edge, then keeps the decision evidence local teams need for security review and incident response.
Peakhour protects citizen portals and agency APIs at the edge, with local evidence for security review.

Public Services Need Resilience That Can Be Explained
Availability During Demand Surges
Election information, emergency updates, licensing, grants, and payment services must absorb flash crowds and hostile traffic without pushing citizens into outages.
Security for Exposed Applications and APIs
Citizen portals, partner integrations, forms, and agency APIs need WAAP, bot, rate, and access controls before requests reach protected systems.
Evidence for Review and Response
Security teams need to show which controls fired, why they fired, what reached origin, and what was exported to agency logging and incident workflows.
The Public-Sector Edge Has to Serve Everyone and Distrust Enough
Public websites cannot assume a neat user population. A normal day can include citizens on old devices, accessibility tools, search crawlers, suppliers, overseas travellers, residential proxies, vulnerability scans, and automated abuse. The control path has to protect services without making legitimate access brittle.
Volatile Demand
Weather events, public announcements, forms opening, and media attention can look like attack traffic until context is attached.
Mixed Application Surfaces
Legacy forms, modern APIs, third-party services, and origin platforms often sit behind the same public service journey.
Accountable Decisions
Blocking an attacker is only part of the job. Agencies also need to explain the decision, preserve access, and feed evidence to operational teams.

A Local Control Plane for Public-Facing Services
Peakhour sits in front of the web and API paths citizens, suppliers, and staff use every day. Requests are evaluated with route, IP, bot, rate, TLS, payload, and application context before they reach the origin service.
For public sector teams, that means the same edge layer can protect high-traffic information pages, authenticated portals, public APIs, and sensitive form submissions while preserving a clear record of each action.
- Local support path: Work with an Australian-owned provider for operational help, tuning, and review of public-service incidents.
- Route-aware controls: Apply different rules to emergency pages, payment paths, authentication routes, uploads, and agency APIs.
- Clean origin delivery: Absorb DDoS pressure and automated abuse before it consumes origin capacity or downstream systems.
- Reviewable evidence: Keep the request signals, policy action, and log destination connected for security and governance teams.

Resilience Is Built From Decisions, Not Just Capacity
Peakhour combines DDoS mitigation, WAAP, bot management, rate controls, origin shielding, and enriched logging so public services can keep serving legitimate users while hostile or abnormal traffic is handled at the edge.
-
Classify Before Origin
Attach reputation, route, rate, bot, protocol, and payload context before requests reach agency applications.
-
Choose a Proportionate Action
Allow, challenge, throttle, block, or log based on the service route and risk, instead of applying one blunt rule to every public request.
-
Export the Evidence
Send actioned request records into agency logging, SIEM, incident, and compliance workflows with the decision context still attached.
DDoS Defence for Essential Digital Services
Public services can be targeted directly or overwhelmed by real-world events. Peakhour absorbs volumetric and Layer 7 pressure at the edge, then uses anomaly detection, rate limits, bot signals, WAAP checks, and origin shielding to keep clean traffic moving.
The operating goal is simple: citizens still reach the information, form, payment, or service status page they need, while agency teams can see what was mitigated and what reached origin.

Security Controls That Match Agency Workflows
Government security teams often inherit mixed technology: legacy pages, modern citizen portals, cloud APIs, vendor services, and internal publishing workflows. Peakhour lets teams map controls to those routes without forcing every service through the same risk treatment.
- WAAP protection: Block common application attacks and suspicious payloads before they reach public-facing services.
- API security: Protect REST, GraphQL, authentication, search, and form endpoints with route-level policy and request evidence.
- Bot and rate controls: Reduce credential stuffing, scraping, scan noise, SMS or form abuse, and automated load on origin systems.
- Access and origin shielding: Limit direct origin exposure and keep administrative or partner paths under tighter control.

Evidence That Stays Useful After the Incident
Public-sector resilience depends on what teams can prove after traffic has been handled. Peakhour keeps operational evidence connected to local support, security review, and agency reporting workflows.
-
Security operations: Review which signals triggered blocks, challenges, throttles, or allow decisions during live traffic.
-
Incident response: Separate attack traffic, flash crowd behaviour, and origin-side issues with request evidence attached.
-
Governance teams: Support Essential Eight, risk, and supplier discussions with concrete control records rather than generic security claims.
-
Digital service owners: Tune controls around citizen experience, accessibility, search indexing, and high-demand service windows.

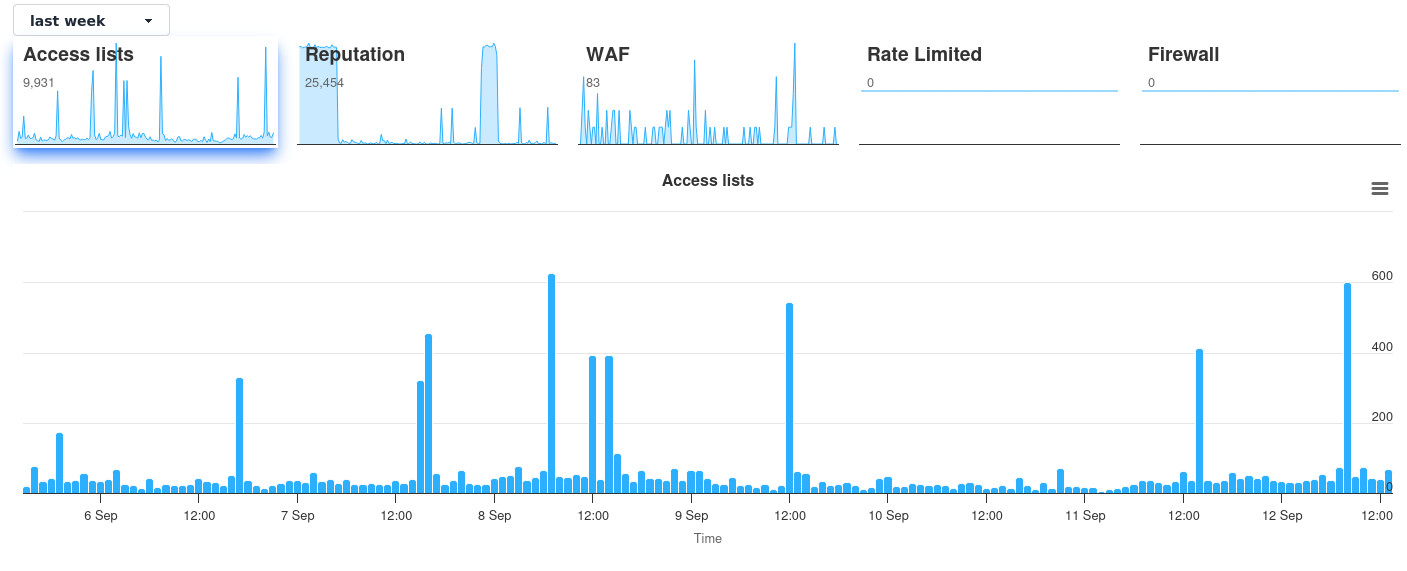
Dashboard Evidence Supports the Control Story
Screenshots are most useful once the architecture is clear. Peakhour dashboards give operators a view of policy actions, noisy routes, attack timing, and request evidence that can support investigation and tuning.
The dashboard supports the public-sector story: controls are applied before origin, evidence is retained, and agency teams can review what happened under pressure.
Map Your Public Service Paths to Edge Controls
Start with the citizen journeys and agency APIs that must stay available, then define the DDoS, WAAP, bot, rate, access, and evidence controls each path needs.