Keep Player Accounts, Game APIs, and Live Services Under Control
Peakhour protects the traffic around online games: login and account flows, inventory and marketplace APIs, automation-heavy gameplay paths, and Layer 7 attacks that try to interrupt launches, tournaments, and peak events.
Protect login, marketplace, API, and live service traffic from account abuse, bots, and availability attacks.

Where Gaming Platforms Lose Control
Player Account Abuse
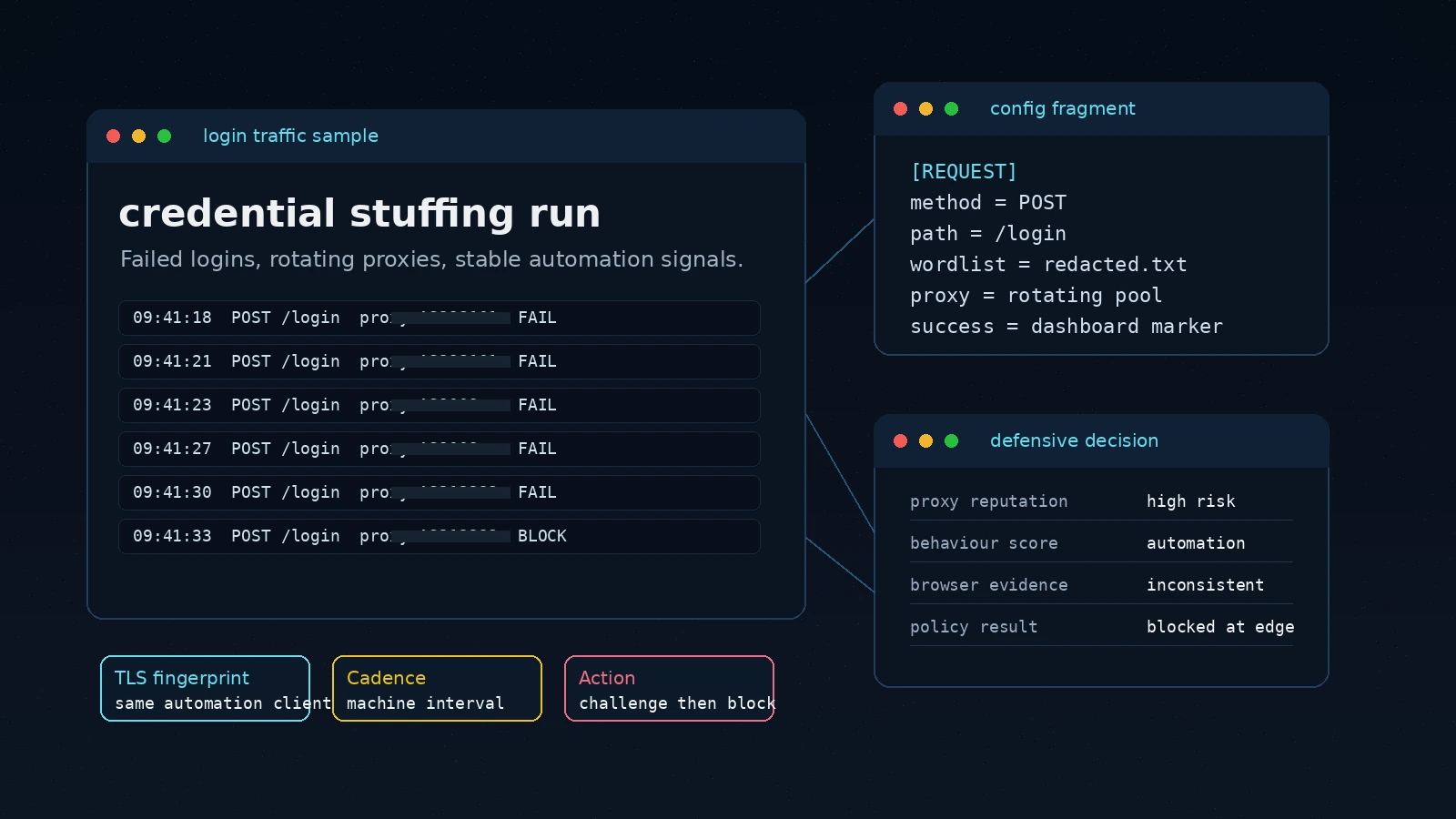
Credential stuffing and scripted login attempts target accounts with purchased content, progression, saved payment details, and reputation inside the player community.
Scripted Play and Economy Abuse
Bots farm resources, reserve limited drops, scrape marketplaces, and automate actions against game APIs that were built for official clients.
Availability Pressure
Launches, patches, esports events, and seasonal traffic can be used as cover for Layer 7 floods against login, matchmaking, store, and API routes.
Abuse Moves Through the Same Routes Players Need
Gaming traffic is difficult to protect with broad blocks because the same service surface carries account access, game-client calls, item transactions, social features, and live-event traffic. Peakhour evaluates route, identity, fingerprint, cadence, bot, rate, and WAAP context before abusive requests reach the service layer.
Login Risk Changes Quickly
Breached credential tests, low-and-slow brute force, and residential proxy rotation need scoring that can tighten around risky account actions without slowing every player.
Unofficial Clients Hit Real APIs
Cheats, farming bots, inventory tools, and marketplace scripts often bypass normal UI paths, so controls need request evidence beyond a user agent or IP address.
Mitigation Must Preserve Play
Availability controls need to absorb attack traffic while keeping clean login, matchmaking, store, and gameplay-support requests moving through the edge.

Defend Accounts Before They Become Player Support Incidents
Peakhour combines Breached Credential Scanning, bot scoring, residential proxy detection, rate controls, and request evidence to protect login, password reset, account recovery, payment, and profile routes.
Risky sessions can be challenged, throttled, blocked, or logged with context, while trusted players keep the low-friction path into the game.

Separate Official Clients from Scripted Automation
Cheats and economy abuse often appear as API traffic: repeated inventory actions, marketplace sweeps, resource farming, session replay, or calls from unauthorized tools.
Bot Management evaluates browser, network, behavioural, route, and cadence signals so suspected automation can be challenged or blocked before it distorts gameplay, item access, or marketplace prices.

Keep Login, Matchmaking, and Game APIs Available Under Attack
Layer 7 floods against login, matchmaking, store, and API routes can look like peak player demand until origin systems are already under pressure. Peakhour applies anomaly detection, advanced network fingerprinting, bot signals, WAAP context, and intelligent rate limits at the edge.
Attack traffic is shaped before it consumes game-service capacity, while operators retain evidence about the pressure, decision path, and clean player delivery.

Game Operations Can See What Changed
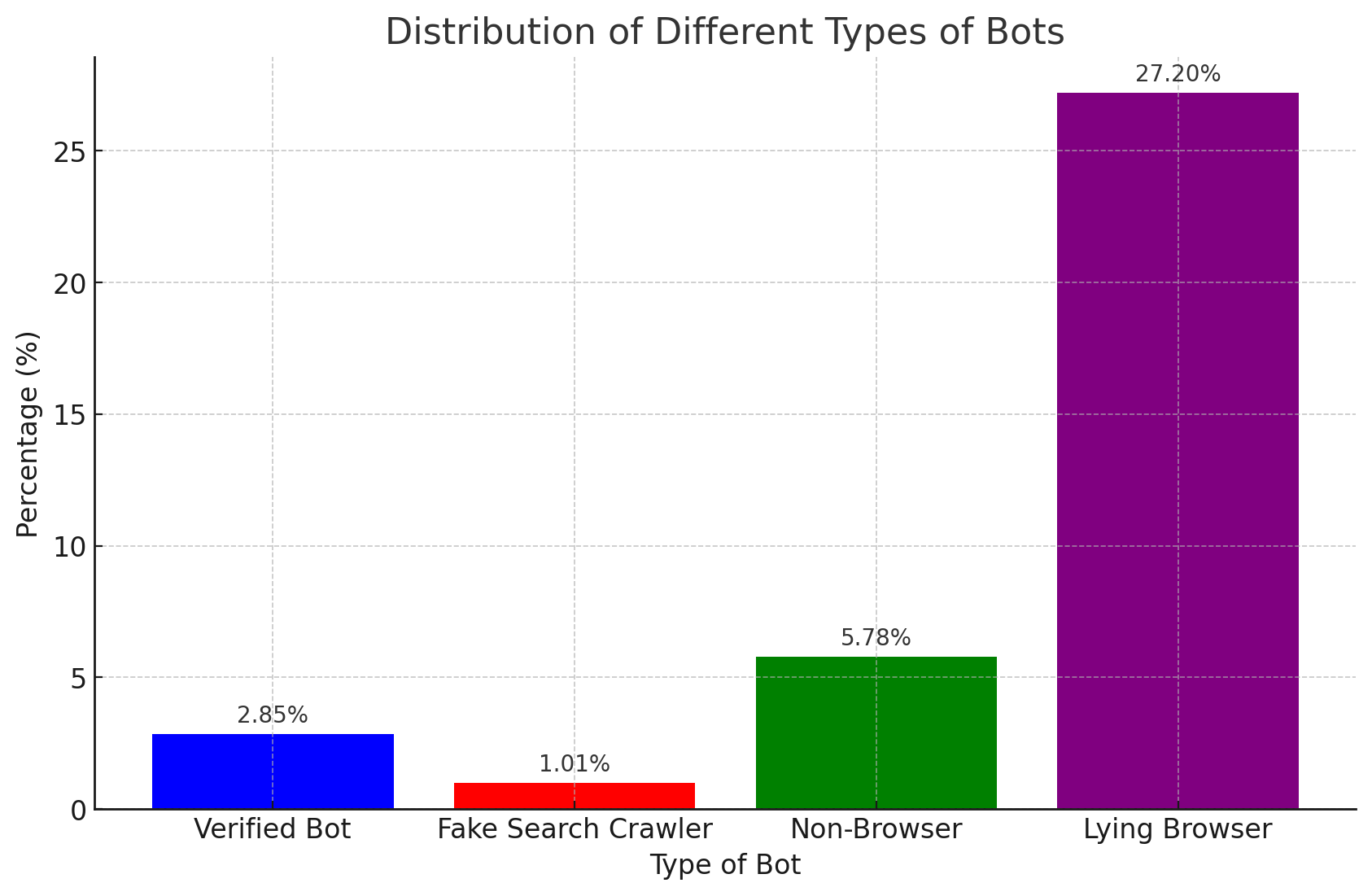
Roadmap visuals explain how abusive traffic is evaluated. Dashboard evidence then confirms production behavior: bot categories, mitigation actions, route pressure, and trend movement during normal play, releases, and live events.
The evidence view gives security, platform, and game operations teams a shared record of signals, actions, and service outcomes without making screenshots carry the page story.
Protect the Player Journey Without Hiding the Evidence
Bring account protection, bot control, API security, and Layer 7 availability into one edge decision path for gaming services.

Relevant information from our blog
The Rise of OpenBullet: Automation Tool or Cybersecurity Threat?
A comprehensive look at OpenBullet, its capabilities, and the implications for cybersecurity in the face of its misuse.
Read More
Bad Bot Countermeasures
Bad bots can significantly impact your website and are hard to detect. Here we detail best practice on how to combat the growing threat from bad bots.
Read More
Residential Proxies, Friend or Foe?
This article explores the world of residential proxies, revealing the challenges and ethical questions they pose in our GeoIP-dependent digital landscape.
Read More