Detect and Stop Automated API Abuse
Detect automation campaigns as they build across login, token, cart, checkout, and account journeys, then apply scoped edge controls that reduce fraud, Layer 7 pressure, and account abuse while trusted clients keep moving.

Recognise Bot Campaigns Before They Become Incidents
API bot abuse behaves like a campaign. The same automation profile can test credentials, rotate residential proxies, change device fingerprints, scrape product data, and push Layer 7 pressure until a workflow gives way.
Credential and Session Abuse
Bots replay leaked credentials, cycle token grants, and test MFA bypass patterns across account and checkout endpoints.
Low-and-Slow Enumeration
Distributed agents mimic normal clients while profiling product, pricing, or account data through repeated API reads.
Automation Against Business Logic
Bots exploit reservation, coupon, order, and pricing workflows to drain inventory, waste discounts, and skew commercial outcomes.

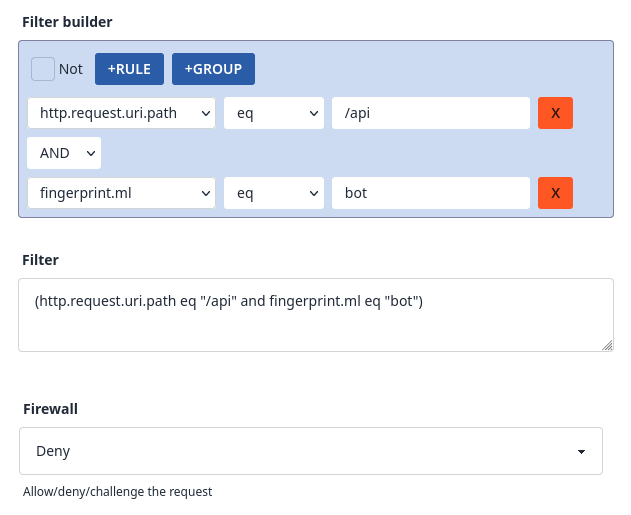
Turn Bot Signals into Targeted API Actions
The behaviour map shows how the campaign forms. Dashboard evidence confirms which proxy, fingerprint, cadence, and route signals triggered action, which API journeys were protected, and which legitimate clients stayed clear of friction.
API bot protection stays focused on campaign detection and mitigation decisions, then feeds the broader API security and traffic-quality workflow when endpoint governance or DDoS response needs to take over.
What Teams Gain from API Bot Protection
Lower Fraud Losses
Reduce account takeover, promo abuse, and automated transaction fraud tied to API workflows.
Reduce DDoS and Origin Pressure
Keep latency and origin load stable by curbing abusive API bursts and Layer 7 request pressure before it scales.
Faster Incident Response
Move from alert to action quickly with request evidence that shows the route, signal, action, and account or fraud impact.
Related evidence
API Bot Abuse Reduced in Production
Customer examples that connect Peakhour controls to production outcomes.
Extend Protection Across API Abuse Paths
Verified Browser Trust
For browser-backed API journeys, separate trusted browser sessions from scripts replaying token, cart, login, or account request shape.
API Protection Platform
Move from bot campaign control into endpoint discovery, schema validation, route evidence, and API governance.
Account Takeover Prevention
Use credential, proxy, device, and behaviour signals to stop automated account abuse before sensitive actions continue.
Online Fraud Prevention
Connect API automation signals to fraud controls for promo abuse, checkout manipulation, and invalid traffic.
DDoS Mitigation
Bring Layer 7 flood pressure into the same edge response path as bot, rate, and WAAP controls.
Protect Critical API Journeys from Bot Abuse

Relevant information from our blog

Advanced Rate Limiting for API Security
How advanced rate limiting protects modern applications and APIs from sophisticated threats.
Read More
Headless Commerce Security: API Protection for Modern E-commerce Architectures
Comprehensive analysis of security challenges in headless commerce and Single Page Applications.
Read More
When Bots Are Your Primary Users
An exploration of how AI agents are reshaping API design principles and why we must evolve our approach to serve both machine and human consumers.
Read More
Residential Proxies, Friend or Foe?
Understand how rotating residential proxy traffic masks automated behaviour and what detection signals matter most.
Read More
Price transparency needs governed automation
Price comparison increasingly depends on current web and API data. See how governed automation separates intended access from abusive extraction.
Read More