Trend movement: Confirm operational impact after controls are applied.
See Where Bot Exposure Starts and What to Fix First
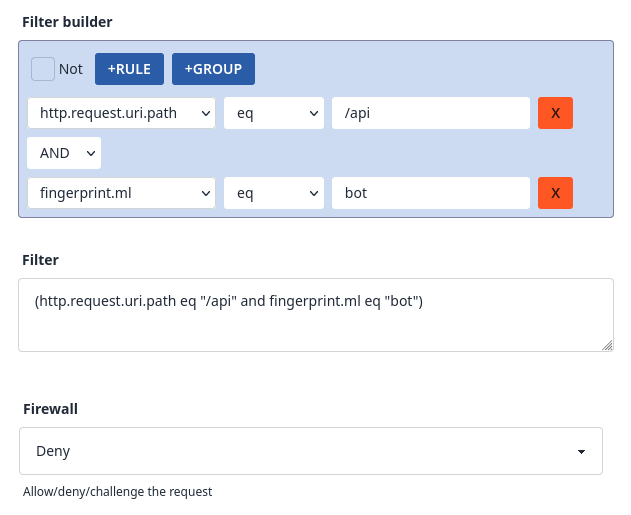
Review fingerprint evidence, request behaviour, and scraper signatures, then receive a scored assessment with practical allow, challenge, and block recommendations.

Where Bot Pressure Is Already Hitting Your Application
Malicious automation now blends credential stuffing, scraping, and surge traffic patterns that look legitimate at first glance. The health check isolates these patterns before they become outages, fraud losses, or data leakage.
Data Breaches
Bots can lead to unauthorised access and data theft through credential stuffing and API attacks, resulting in regulatory penalties and permanent loss of customer trust.
Service Disruption
DoS attacks can crash websites during critical sales periods, leading to immediate revenue loss and lasting reputational damage that affects future business growth.
Economic Impact
Web scraping undermines competitive advantage by exposing pricing strategies; scalping bots cause direct revenue loss and customer frustration that damages brand loyalty.

Assessment Flow from Signal Review to Control Plan
Peakhour runs a structured assessment across request signals, automation behaviour, and business impact, then maps findings to a control path that can run through Peakhour Edge or alongside your existing CDN or edge.
-
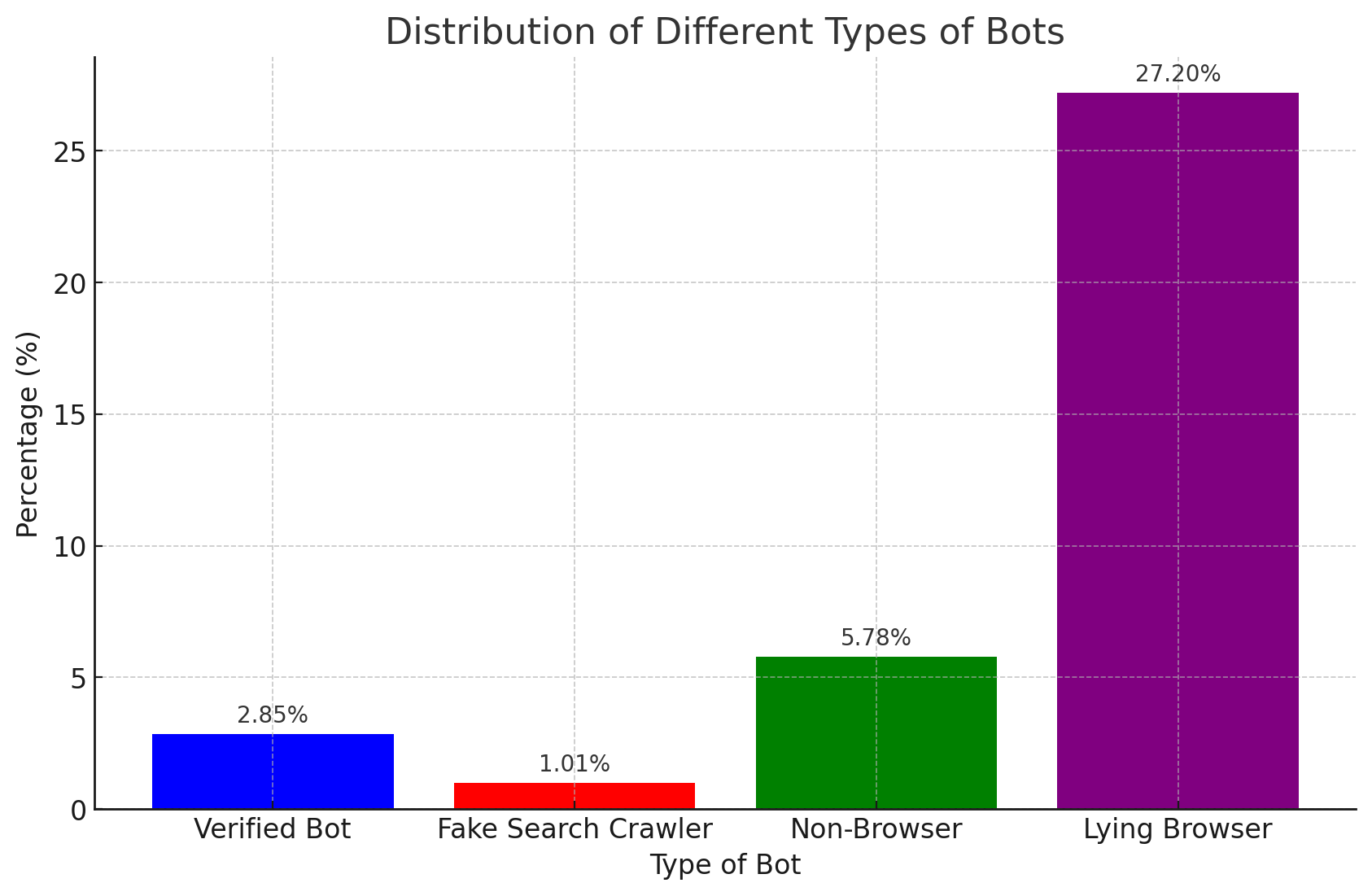
Traffic composition review
Measure how much of your traffic is automated and where abuse is concentrated.
-
Credential attack analysis
Identify takeover and login abuse signatures that increase account risk.
-
Scraping and scalping fingerprinting
Separate purchase-intent users from scraper and scalper automation.
-
Recommended policy actions
Receive clear allow, challenge, and block actions matched to observed bot behaviour.
Operational Evidence in the Dashboard
Assessment findings are validated in production telemetry. This proof view ties bot categories, mitigation actions, and trend movement together so operations teams can confirm what changed after controls are applied.
Assessment proof: Keep screenshots as evidence that supports the scorecard and recommendation path.
What You Get from the Health Check
Expert Consultation
Work directly with security specialists who review your bot risk profile and current edge posture.
Latest Technology
Use advanced detection and telemetry tooling to diagnose request-level bot behaviour.
Structured Approach
Follow a clear sequence from kickoff and audit to findings review and implementation planning.
Actionable Recommendations
Receive direct, practical actions to reduce current bot exposure and ongoing risk.
Flexible & Affordable
Choose full-service or managed support based on your team model and operating cadence.
Related evidence
Bot Exposure Reduced in Production
Customer examples that connect Peakhour controls to production outcomes.

Gumtree
Improving Traffic Quality and Reclaiming Platform Control
Gumtree, Australia's leading marketplace, battled significant bot traffic that skewed analytics, enabled scammers, and increased infrastructure costs. Peakhour's bot management solution improved the origin traffic mix, cleaned up campaign analytics, protected A/B testing data, and created a new revenue stream.

Pharmacy Direct
Healthcare Security & Bot Protection Case Study
How Australia's first online pharmacy secured patient data and prevented healthcare fraud with advanced bot protection whilst saving their $900k platform investment.
Dive Deeper into Bot Security
Understanding Internet Bots
Learn about the various types of bots and their impact on web applications.
Types of Malicious Bots
Explore the different categories of malicious bots and their specific threats.
Bot Traffic Statistics
Discover eye-opening statistics about bot traffic and its impact on websites.
Secure Your Web Applications Today

Relevant information from our blog

When Bots Break Bad
Even 'good' bots can end up abusing your site and impacting performance, learn why and how to stop it.
Read More
Malicious Bot Threats: Enterprise Security Challenges for Modern Applications
Comprehensive analysis of malicious bot threats targeting modern applications and APIs.
Read More
Enterprise Bot Management: Advanced Threat Protection for Application Security
Comprehensive guide to enterprise bot management for modern application security platforms.
Read More