Keep Listings, Sellers, and Buyers Worth Trusting
Classifieds platforms need to stop fake ads, account takeover, scraping, and automated spam without slowing real sellers, buyers, search traffic, or moderation teams.

Abuse Patterns That Damage Marketplace Trust
Listing Harvesting
Scrapers enumerate search, category, price, vehicle, property, and seller pages so they can copy inventory and competitive signals outside your platform.
Fake Ads and Seller Scams
Automation can create disposable accounts, post fraudulent listings, spam buyers, and push moderation queues past the point where manual review can keep up.
Account Takeover
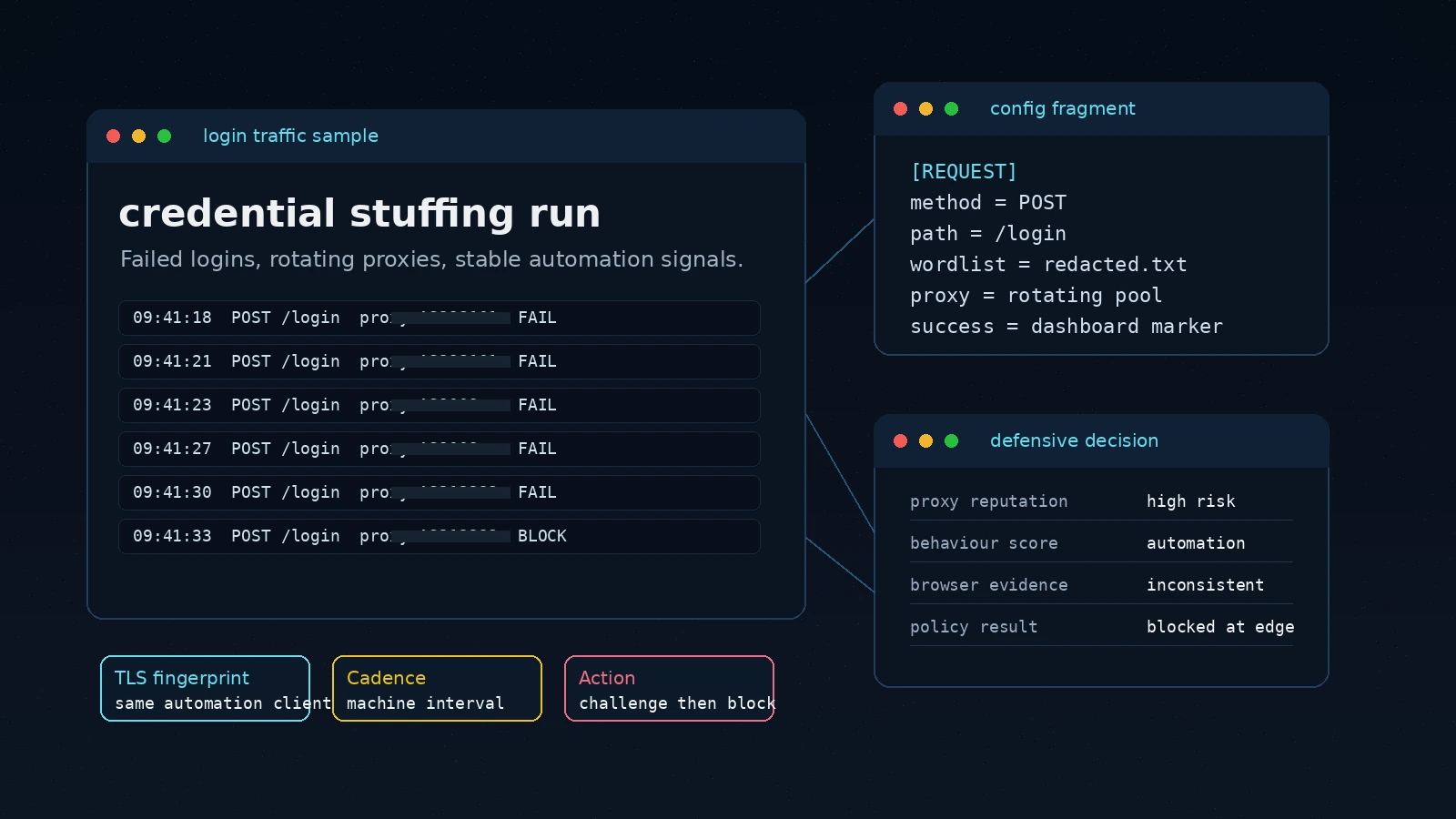
Credential stuffing gives attackers access to trusted seller identities, buyer messages, saved payment flows, and reputation that took years to build.
Marketplace Abuse Moves Across Search, Posting, Login, and Messaging
A classifieds attack rarely stays in one lane. The same operator may scrape search pages, test credentials, create seller accounts, post fake ads, and use messages to move victims off-platform. Peakhour links those signals before they become a moderation incident.
High-Value Routes Need Context
Search, listing detail, posting, login, and message routes each expose different risks, so edge policy needs route-aware evidence rather than one blanket rule.
Bad Automation Looks Distributed
Residential proxies, low-volume credential tests, and slow listing harvests can appear ordinary until cadence, fingerprint, account, and route signals are correlated.
Moderation Needs Cleaner Inputs
Security controls should reduce fake submissions and account abuse before reviewers spend time on listings, sellers, and messages that automation should never have created.

Protect Listing Data Without Hiding It from Real Buyers
Peakhour's Bot Management evaluates listing access by request cadence, browser and network fingerprints, route mix, session history, and known automation signals.
Trusted buyers keep searching. Suspicious collectors can be challenged, rate-limited, or blocked before they copy inventory, pricing, location, and seller data at scale.

Stop Fake Listings Before They Reach the Queue
Posting flows need stricter evidence than browsing flows. Peakhour combines IP intelligence, residential proxy detection, device signals, behaviour, and rate limits to find automated submissions before they become live ads.
That lets moderation focus on judgement calls instead of bulk cleanup from scripted seller accounts, repeated descriptions, and throwaway contact patterns.

Defend Trusted Seller Accounts and Buyer Messages
Reputation is part of marketplace inventory. Peakhour helps protect seller and buyer accounts from credential stuffing, brute-force login attempts, and scripted session abuse.
Breached Credential Scanning, bot scoring, and risk-based controls keep compromised credentials from turning into fraudulent listings, payment redirection, or scam messages.

Operational Evidence Supports the Abuse Decision
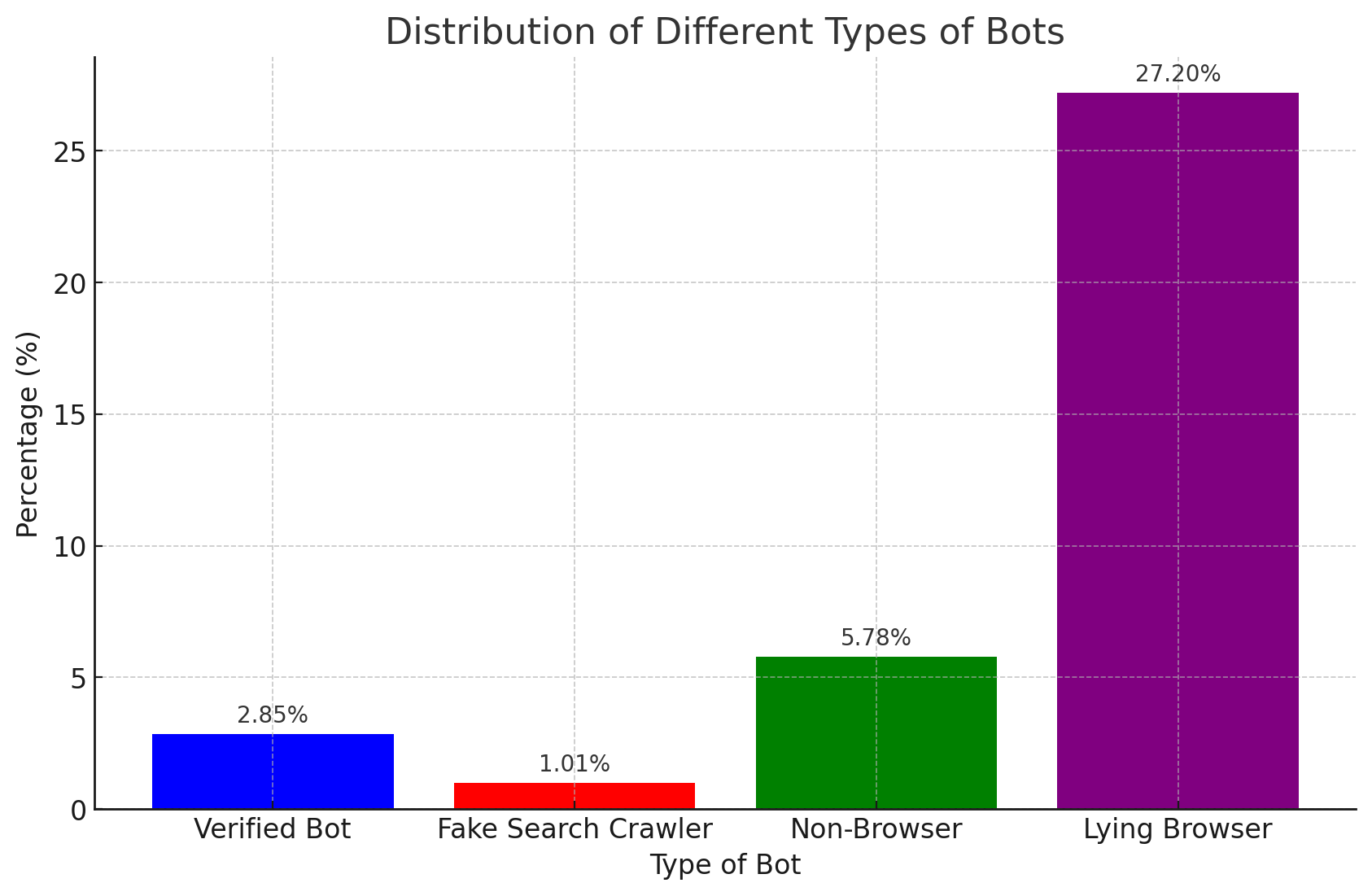
Roadmap visuals explain the control path; dashboard evidence shows whether the marketplace policy is working. Teams can review bot categories, action mix, route pressure, and trend movement without making a raw screenshot carry the whole page.
The evidence view connects marketplace routes, bot signals, and actions so operators can tune policy without penalising legitimate buyers and sellers.
Turn Marketplace Abuse Signals Into Cleaner Listings
Bring scraping, fake listing, login, and messaging abuse into one edge decision path with evidence your security, product, and moderation teams can use.

Relevant information from our blog
The Rise of OpenBullet: Automation Tool or Cybersecurity Threat?
A comprehensive look at OpenBullet, its capabilities, and the implications for cybersecurity in the face of its misuse.
Read More
Bad Bot Countermeasures
Bad bots can significantly impact your website and are hard to detect. Here we detail best practice on how to combat the growing threat from bad bots.
Read More
The Iconic is the latest Account Takeover victim in the news
Popular Australian fashion website TheIconic recently suffered reputational damage from fraudsters placing orders after an account takeover. Learn how this happens and what you can do to stop it.
Read More