Decision stream: Track allow, deny, and challenge outcomes for each protected route.
Zero Trust Access at the edge
Evaluate every application request against identity, device context, certificate state, and policy before forwarding approved traffic over an encrypted path.

Access Requests Arrive Faster Than Legacy Network Controls Can Explain
IP, VPN, and location-based controls admit users to network space instead of proving each application request. Teams are then left reconciling identity events, device posture, and request logs across separate systems.
Network Admission Is Broader Than Request Intent
Legacy VPN flows connect users to network ranges instead of validating each request. Once connected, identity, device posture, and application intent are no longer evaluated together.
Identity Events Are Not Enough for Investigation
Login events alone do not show which protected route was requested, which policy was evaluated, or which denied request requires follow-up.
VPN Friction Slows Teams and Increases Support Load
When secure access depends on heavy VPN clients, remote staff and contractors hit avoidable latency and reliability issues that pull operations teams into avoidable support work.

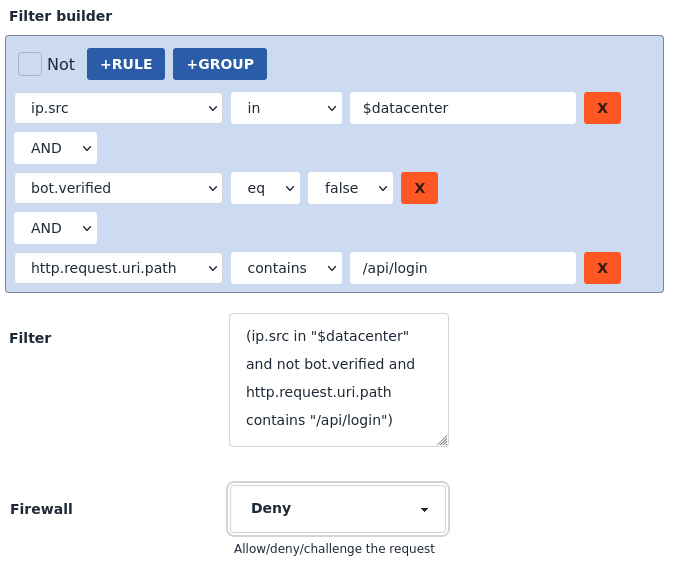
Policy Decisions Happen on Every Request Before Origin Access
Peakhour's Zero Trust Access replaces broad network admission with per-request policy decisions at the edge. Approved requests continue over an encrypted path, while denied or challenged decisions remain visible for audit and SIEM analysis.
-
Apply One Access Model Across SaaS, Cloud, and On-Prem
Peakhour is identity and origin agnostic, so corporate and SaaS applications can share one governed request decision path.
-
Evaluate Identity, Device, and Route Context Together
Control access by checking identity with device posture, location, IP range, MFA method, certificate state, and application path on each request.
-
Capture Request Evidence for Audit and Response
Log each protected request and forward enriched access events to SIEM and analysis tools for faster investigation and audit reporting.
Operational Proof for Access Decisions and Audit Readiness
The access flow diagrams establish how requests are evaluated. Dashboard evidence confirms the live policy state, route outcomes, and request telemetry needed for incident response and compliance review.
Compliance workflow: Prove who requested what, which policy handled it, and where the decision was recorded.

Explore Our Security Platform
Replace Your VPN with a Modern Zero Trust Solution

Relevant information from our blog

ModSecurity's End-of-Life: Implications for Peakhour and Customers
ModSecurity's end-of-life marks a pivotal moment in application security evolution. Discover how modern Application Security Platforms are advancing beyond traditional WAF approaches.
Read More
APRA Cybersecurity Guidelines: Application Security Requirements for Australian Financial Services
Comprehensive guide to APRA cybersecurity requirements for Australian financial institutions.
Read More
HTTP Security Headers: Essential Browser Protection for Web Application Security
Comprehensive guide to HTTP security headers for protecting web applications from client-side attacks.
Read More