Advanced Rate Limiting
Build precise edge rules from concrete inputs: request path, country, ASN, TLS fingerprint, response code, bot verified status, threshold, interval, and action state. Stop abusive keys while legitimate users continue through.
Advanced Rate Limiting Capabilities
Protect Revenue & Ad Spend
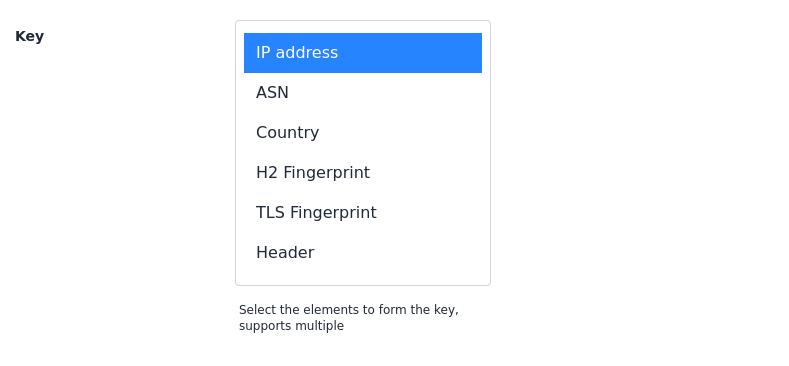
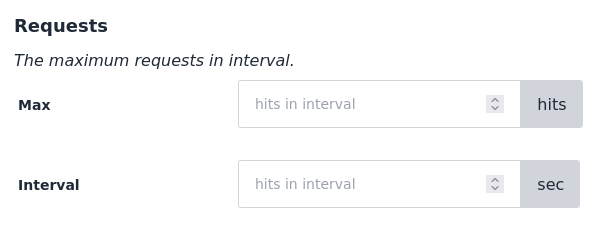
Count requests using keys like path, headers, ASN, country, IP, TLS fingerprint, and response code. Stop malicious traffic that wastes marketing budgets and threatens revenue streams without blocking real customers.
Granular Control
Set filters, request thresholds, enforcement intervals, and action states to match your business logic. Maintain protection against new threats with custom rules for flexible security.
Reduce Operational Costs
Get full protection without hidden costs. Avoid surprise expenses from traffic spikes and attacks while reducing server load and operational overhead with no limits on traffic protection.
Modern Attackers Evade Basic Limits
Websites and APIs face threats from bots, scrapers, and malicious users. Traditional IP-based rate limiting falls short when attackers rotate residential proxies, ASNs, countries, TLS fingerprints, and response-code failure loops.
Distributed Attacks
Attackers rotate residential networks, countries, and ASNs to bypass limits that only count IP addresses.
Application Layer Attacks
Layer 7 floods and brute-force attempts create response-code loops that overwhelm login, checkout, and API paths.
API and Content Scraping
Automated tools scrape APIs and content with repeated paths, TLS fingerprints, and unverified bot status.

Model the Actor Before Enforcing
Build the rule in a sequence: isolate sensitive paths, combine network and fingerprint signals, then enforce threshold and action states. This keeps controls precise even when attackers rotate infrastructure.
The policy identifies the real abusive actor without treating every visitor or endpoint the same.
Operational Counters Show the Policy Working
Dashboard evidence validates each deployed policy with allowed, blocked, and threshold-hit counters for the exact key and interval you configured. Teams can confirm that abusive request patterns are being throttled while legitimate traffic remains served.
Operational counters show whether the policy is reducing abuse without interrupting legitimate traffic.
Stronger Protection With Lower Operational Overhead
High-Precision Enforcement
Policies match real attack behavior instead of broad IP ranges, reducing false positives for normal users.
Measurable Risk Reduction
Operational counters provide continuous evidence that abusive traffic is being reduced on targeted endpoints.
Fast Incident Response
Deploy new thresholds and action states quickly when attack patterns shift, without waiting on application releases.
Related evidence
Rate Controls Proven in Production
Customer examples that connect Peakhour controls to production outcomes.

Stone & Chalk
Fintech Hub Enterprise Security
How Australia's leading fintech hub secured hundreds of startups with enterprise-grade application security, zero-day vulnerability protection, and comprehensive threat management.

National Gallery Australia
Government Security Compliance & Bot Management
How Australia's National Gallery achieved government security compliance with advanced bot management, DDoS protection, and content scraping controls whilst improving digital visitor experience.
Josh Sinclair, Head of Product
Explore Related Solutions
Application Security Platform
Discover our holistic approach to application and API security.
Bot Management
Detect and mitigate bot traffic while allowing legitimate users and good bots.
DDoS Mitigation
Protect your infrastructure from volumetric and application layer DDoS attacks.
Secure Your Application Today

Relevant information from our blog

Advanced Rate Limiting for API Security: Protecting Applications from Modern Threats
How advanced rate limiting protects modern applications and APIs from sophisticated threats.
Read More
Rate limiting - How it works
How can rate limiting protect your web application and the key items to consider when enabling.
Read More
Enterprise DDoS Protection: Lessons from Microsoft 365 Attack for Application Security
Analysis of the Microsoft 365 DDoS attack reveals critical lessons for enterprise application security platforms.
Read More