Web Application & API Protection
WAAP Protection
Peakhour evaluates malicious traffic at the edge with WAF rules, API policy, bot signals, rate limits, and DDoS controls, then delivers clean application traffic with evidence for every decision.
Peakhour applies WAF, API, bot, rate limit, and DDoS decisions before clean app delivery and evidence logging.

91%
detection rate
Full
decision context
Flexible
Works with your edge
Threat Traffic Rarely Arrives as a Single Pattern
Credential abuse, malicious automation, and Layer 7 flood traffic often overlap in the same traffic window. WAAP keeps these signals in one decision path so policy can adapt per request instead of relying on a single static rule.
Attack Mix Shifts Fast
Abusive traffic rotates payload shape, endpoint focus, and request cadence to bypass single-control defenses.
Policies Need Context
The right action depends on route sensitivity, user state, request intent, and real-time attack pressure.
Operations Need Confidence
Security teams need to verify that mitigations are working without manually reconstructing why a decision was made.

API Policy and WAF Rules Work as One Control Surface

Layered Mitigation Preserves Clean Delivery


Controls Feed Operational Evidence by Default
Every policy branch writes structured event evidence so responders can correlate attack type, selected control, and delivery outcome in one place.
-
Bot and Abuse Mitigation
Automation signals and behavior profiles feed direct allow, challenge, and block outcomes tied to route-level policy.
-
Rate and IP Intelligence
Rate controls and IP context suppress flood behavior and hostile origins without overblocking trusted customer traffic.
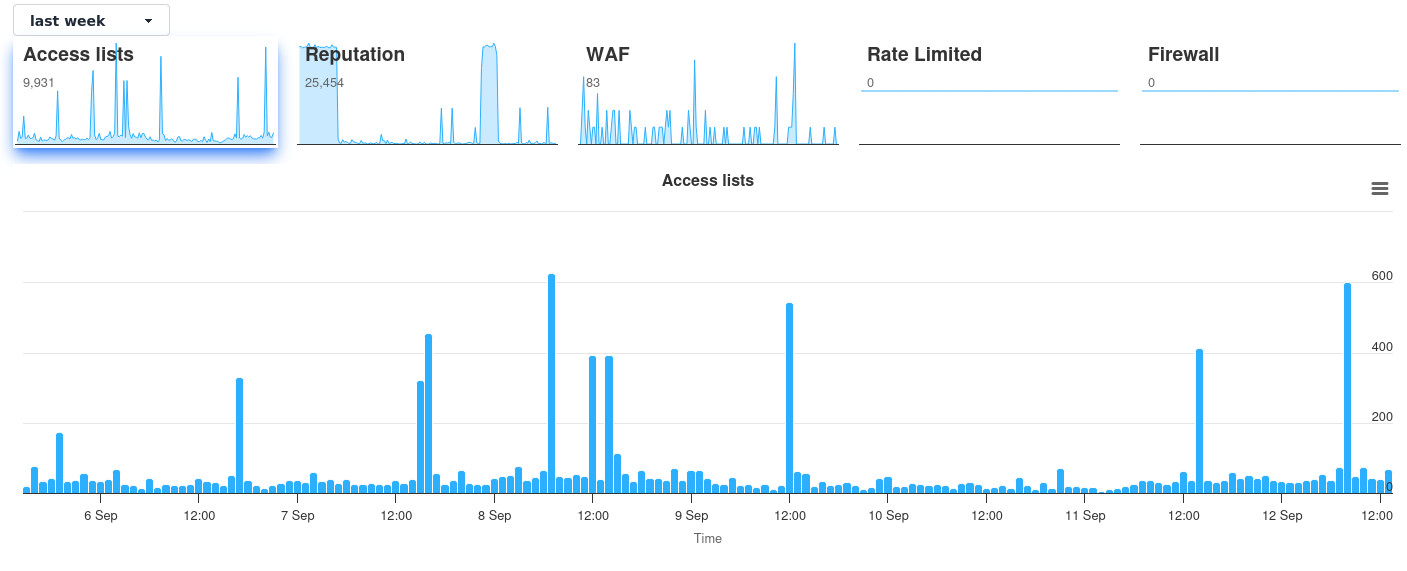
Dashboard Evidence Confirms Policy Behavior in Production
The visual roadmap explains how controls layer together. Dashboard telemetry then proves those controls are acting as intended under live load, with events that security and platform teams can review quickly.
Operational proof remains connected to layered controls, so screenshot evidence supports decision quality instead of replacing the page narrative.
Related evidence
Application Attacks Reduced in Production
Customer examples that connect Peakhour controls to production outcomes.

LegalVision
Scaling with Performance
How Australia's innovative commercial law firm scaled from a two-person startup to 150+ employees whilst becoming the country's #1 online legal service provider.

Stone & Chalk
Fintech Hub Enterprise Security
How Australia's leading fintech hub secured hundreds of startups with enterprise-grade application security, zero-day vulnerability protection, and comprehensive threat management.
Explore Our Security Solutions
Protect Your Web Applications Today

Relevant information from our blog

Protecting the browser, an HTTP security header overview
Client side attacks on your website can have devastating impact on business credibility. Learn how to protect your clients with these HTTP Headers.
Read More
Layer 7 DoS attacks and Full Page Caching
Discover how Full Page Caching can help mitigate layer 7 DoS attacks.
Read More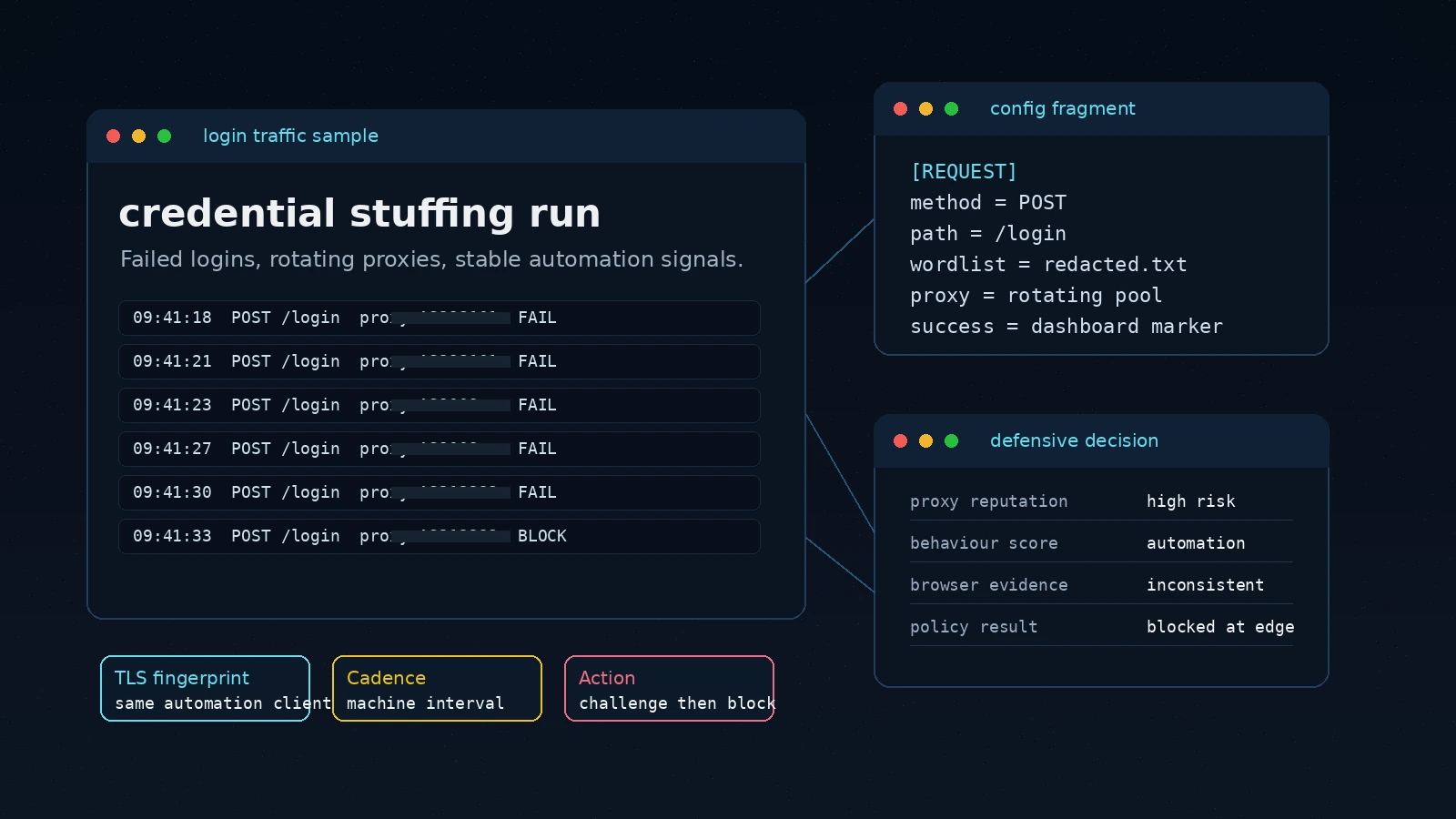
The Rise of OpenBullet: Automation Tool or Cybersecurity Threat?
A comprehensive look at OpenBullet, its capabilities, and the implications for cybersecurity in the face of its misuse.
Read More