DDoS Protection
Absorb high-volume surge traffic at the edge, identify Layer 7 floods with anomaly detection, and keep clean requests moving to the application. Use Peakhour as your edge, or add Peakhour intelligence to the CDN or edge you already run.
Keep Critical Traffic Moving During Layer 7 Attacks
Protect Your Revenue
With our expertise centred on Layer 7, Peakhour's DDoS protection is designed to meticulously safeguard your applications, websites, and web APIs from targeted attacks that could take your business offline and damage customer trust.
Dynamic Adaptation
As cyber threats evolve, so does our defence. Our DDoS protection system adapts to changing attack patterns, ensuring your business continuity without any performance compromise.
Guaranteed Service Availability
Onboard DDoS controls as Peakhour Edge or alongside an existing CDN, with routing, thresholds, alerting, and mitigation records prepared before emergency traffic arrives.
From Attack Surge to Clean Delivery
Peakhour's Layer 7 controls work as one mitigation path: detect abnormal floods, enforce rate and bot decisions, apply WAAP policy, and deliver legitimate traffic to origin while preserving mitigation records.
-
Mitigation for HTTP(S) GET and POST request floods
-
Protection against SlowLoris and other advanced Layer 7 threats
-
Robust defence for intricate attack patterns
-
Real-time threat detection and automatic mitigation
-
Business continuity assurance with guaranteed uptime

Absorb and Shape Flood Traffic at the Edge
When Layer 7 traffic spikes, Peakhour absorbs the surge at the edge and shapes requests before origin capacity is consumed. Teams can define thresholds using network, geography, headers, behavioural attributes, and other request signals instead of relying on IP-only limits.
This keeps distributed floods from overwhelming application infrastructure while legitimate sessions continue through a controlled clean path.

Detect, Decide, and Mitigate in One Control Path
Layer 7 anomaly detection, bot signals, and WAAP context are evaluated together so mitigation can be precise instead of broad. Request classes that match attack behaviour are blocked or challenged while trusted traffic keeps flowing.
The same control path supports rapid tuning during incidents, allowing operators to tighten policy as attack patterns shift without disrupting healthy user traffic.

Layered Controls That Adapt as Attacks Change
Threat intelligence, behavioural analysis, and bot controls are continuously evaluated so new attack signatures can be contained before they propagate across your application surface.
Because these controls run in layers, your team can calibrate defences for login, API, and checkout paths independently while maintaining service continuity through sustained attack windows.

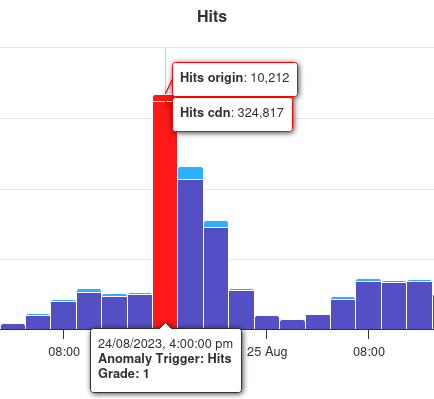
Mitigation Records Confirm Performance
Dashboard telemetry is used as production proof, not as the story itself. Operators can validate that attack traffic is being suppressed while clean requests continue through the protected path.
This mitigation view ties attack visibility, mitigation decisions, and service continuity together for incident response and post-incident review.
Related evidence
DDoS Pressure Reduced in Production
Customer examples that connect Peakhour controls to production outcomes.

Kitchen Warehouse
COVID-19 Traffic Surge Success
How Australia's #1 online kitchenware retailer thrived during COVID-19's unprecedented traffic surge and achieved 150% revenue growth with Peakhour's performance solutions.

Stone & Chalk
Fintech Hub Enterprise Security
How Australia's leading fintech hub secured hundreds of startups with enterprise-grade application security, zero-day vulnerability protection, and comprehensive threat management.
Connect DDoS Protection to Adjacent Controls
DDoS Mitigation Platform
Plan the edge-action workflow for detection, challenge, throttle, block, clean delivery, and review.
Bot Management
Use bot scores, fingerprints, proxy signals, and behaviour to identify automated Layer 7 pressure.
WAAP and WAF Controls
Combine flood response with WAF, API, bot, and rate policy in one operating path.
Load Balancing
Keep clean traffic moving to healthy origins while mitigation absorbs abusive traffic at the edge.
Origin Shield
Reduce dynamic origin exposure when attacks target costly pages, APIs, or cache-miss paths.
Protect Your Applications from DDoS Attacks

Relevant information from our blog

Layer 7 DoS attacks and Full Page Caching
Discover how Full Page Caching can help mitigate layer 7 DoS attacks.
Read More
Understanding the HTTP/2 Rapid Reset Attack: What It Means and How to Stay Protected
A comprehensive breakdown of the HTTP/2 Rapid Reset flaw and guidance on bolstering defences against potential DDoS attacks.
Read More
HTTP/2 Rapid Reset Attack Deepdive
The technicalities of the HTTP/2 Rapid Reset vulnerability and steps to fortify against DDoS threats.
Read More